Given the current state of IT security, traditional anti-virus software installed on endpoints is not nearly as effective as it once might have been. In recognition of that new reality, Sophos today launched a next-generation endpoint security offering that enables IT organizations to address zero-day attacks as well as various forms of ransomware in a matter of seconds.
While no one has come up with a foolproof method for preventing these types of attacks from infecting endpoints, Sophos CTO Joe Levy says a lot more can be done to limit their potential impact on the organization.
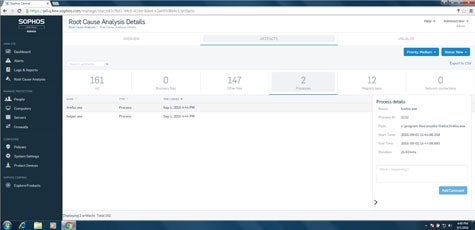
Levy says Sophos Intercept X makes use of Big Data analytics applications developed by Sophos to detect these potential threats in a way that enables IT organizations to then quarantine a system in a matter of seconds.
IT administrators can then make use of a Sophos Clean module included in Sophos Intercept X to remove the offending piece of malware. In addition, Sophos is including a CryptoGuard module that detects when files are being encrypted. Once that detection is made, CryptoGuard creates an unencrypted copy of that file to make sure that the amount of data that an IT organization can lose to these types of attacks is kept to a bare minimum.
Sophos Intercept X is effective, says Levy, because Sophos has decided to focus on the techniques hackers use to deliver malware. While there are hundreds of millions of variants of malware, Levy says, it turns out hackers use only a couple of dozen techniques to deliver them. Sophos Intercept X is designed to identify those techniques in a way that not only leads to the discovery of malware much faster, but also to identifying the source of the attack.
“We’re reducing the dwell time for malware,” says Levy.
Malware often lies undetected for weeks, even months. Levy says Sophos Intercept X can be deployed on top of both Sophos and third-party anti-virus software to provide a much more robust level of endpoint security than what any existing AV software is capable of providing by relying on malware signatures.
There’s no doubt that IT security professionals have been taking it on the chin these past few months. As attacks become more sophisticated, detecting them has become more challenging than ever. Once inside an organization, those attacks are a lot more debilitating. It’s clear a new approach to defending endpoints, the primary focus of most of those attacks, is now required.