Ping Identity might be on your list of potential IAM software solutions. It was designed for hybrid environments, so it will suit your needs regardless of what kinds of applications you use. It also offers a number of unique capabilities, including multi-factor authentication (MFA), single sign-on (SSO), fraud detection, and orchestration.
You can use Ping Identity to create seamless and secure sign on experiences for your customers and employees alike, but how do you know if it’s the right fit for your organization? Consider your needs while reading our overview of Ping Identity’s features and pricing.
Jump to:
Ping Identity Features
Ping Identity can be tailored specifically for customers, partners, and employees. However, the platform as a whole includes a few core features that help register, verify, authenticate, authorize, and monitor all users across your entire system.
Register
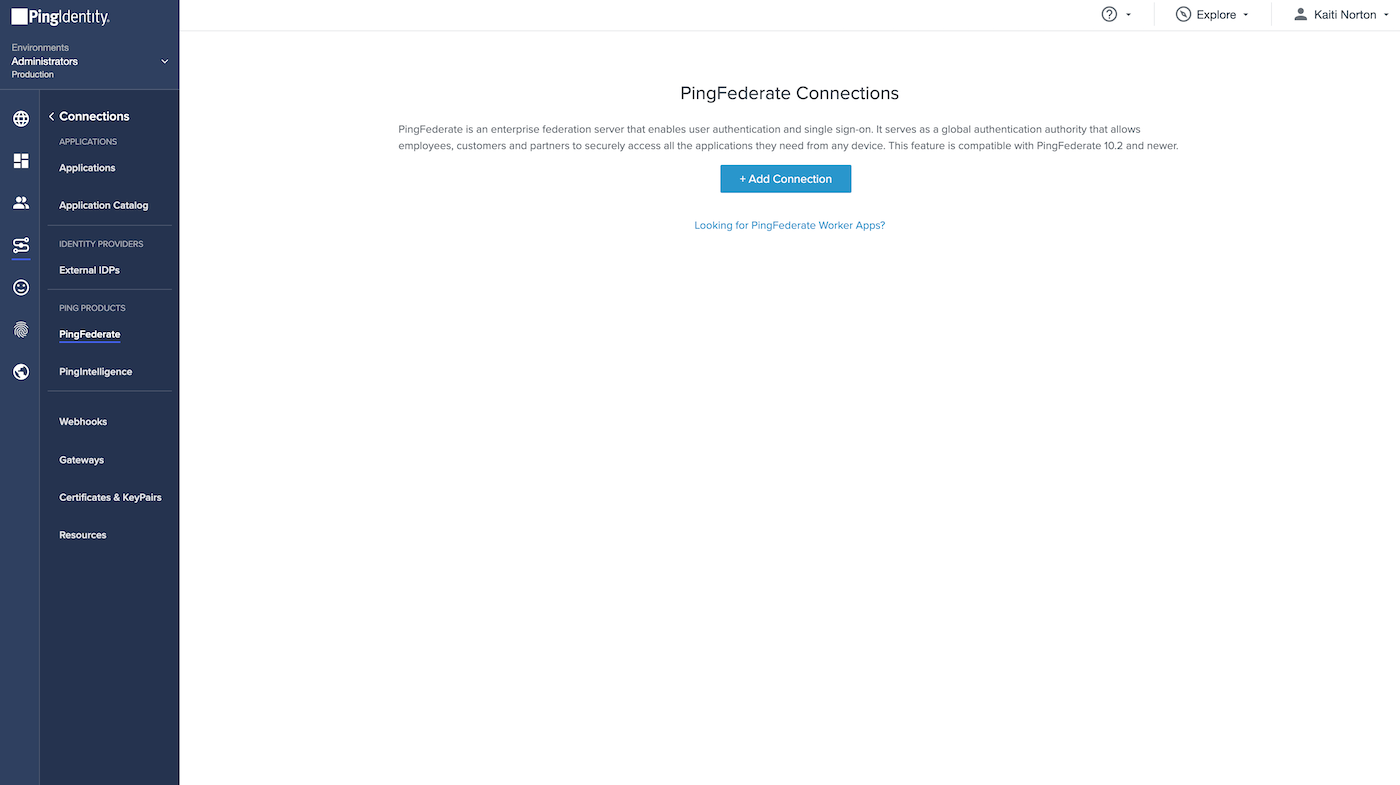
Ping Identity functions as a federation hub to provide SSO capabilities across multiple service and identity providers. It supports a number of different standards including OpenID Connect, OAuth, SAML, WS-Federation, WS-Trust, and SCIM among others. Then, the Ping Identity directory aggregates identity and profile data from a variety of technologies, encrypts it, and protects it from external and insider attacks.
Verify
The identity verification features embedded in the Ping Identity platform are relatively straightforward. Each new user is required to submit a copy of their photo ID and a photo captured in real time using their device’s camera. This information is then cross-referenced to confirm that each user is who they claim to be.
If a user needs to create additional accounts, Ping Identity registers their identity details with their device so they don’t have to go through the verification process again. This improves the user experience on the front end and prevents duplicate records on the back end.
Authenticate
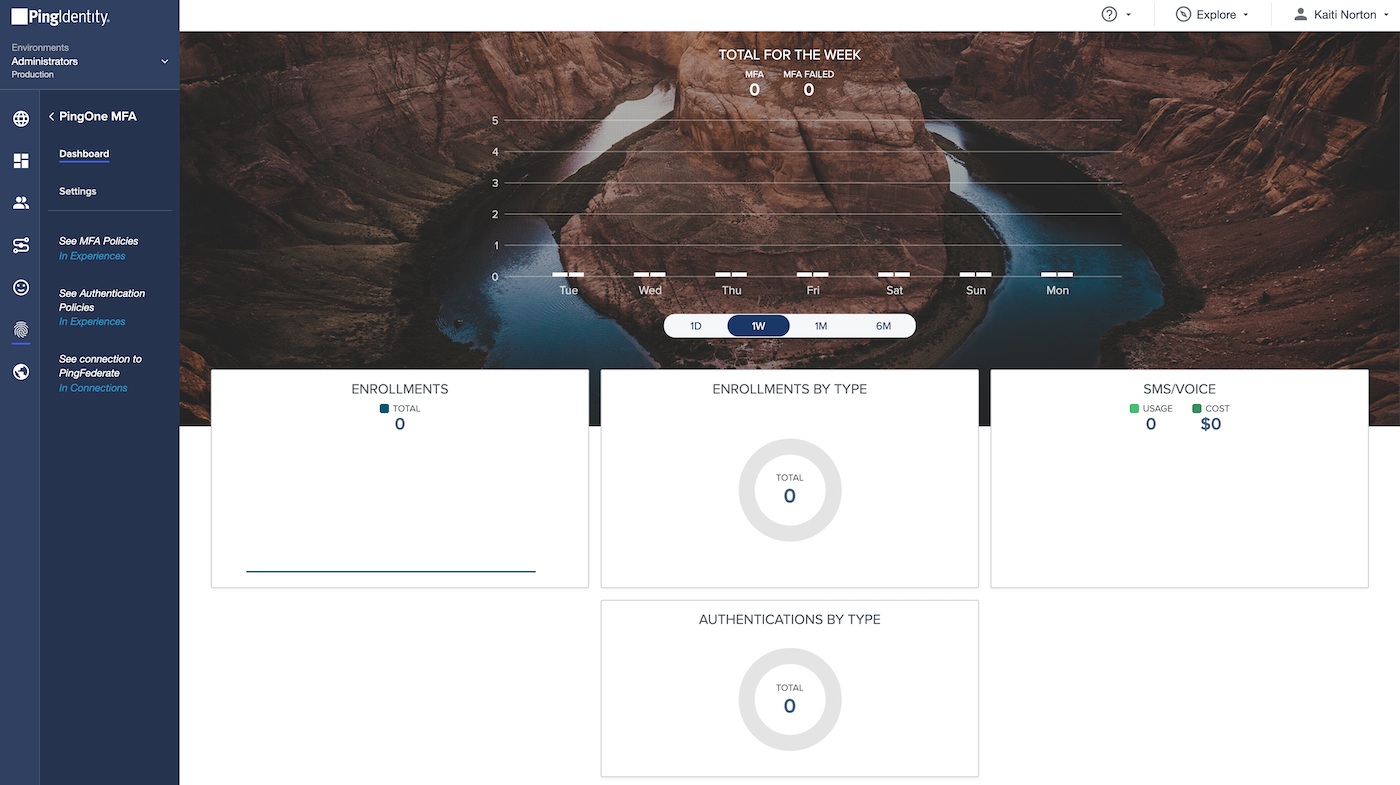
An MFA feature is a must-have for any viable IAM platform, but Ping Identity takes it one step further. Ping uses adaptive authentication, which takes into consideration the user’s contextual and behavioral details like geolocation and the length of time since they last logged in. Adaptive authentication adds an extra layer of security to keep unrecognized users out while also making access easier and safer for legitimate users.
Furthermore, Ping Identity supports passwordless authentication. This cutting edge technology altogether eliminates one of the biggest security vulnerabilities: weak passwords. Instead, Ping uses advanced authentication mechanisms to create a stronger yet simpler login experience.
Authorize
Once registered users have been verified and authenticated, Ping Identity then allows you to authorize users for the appropriate levels of access to your systems. Authorization controls are crucial for compliance with consumer data regulations, and Ping offers dynamic authorization to make context-driven access decisions in real time. The fine-grained attribute-based access controls are precisely what enterprises need to maintain agility while also preserving compliance.
Monitor
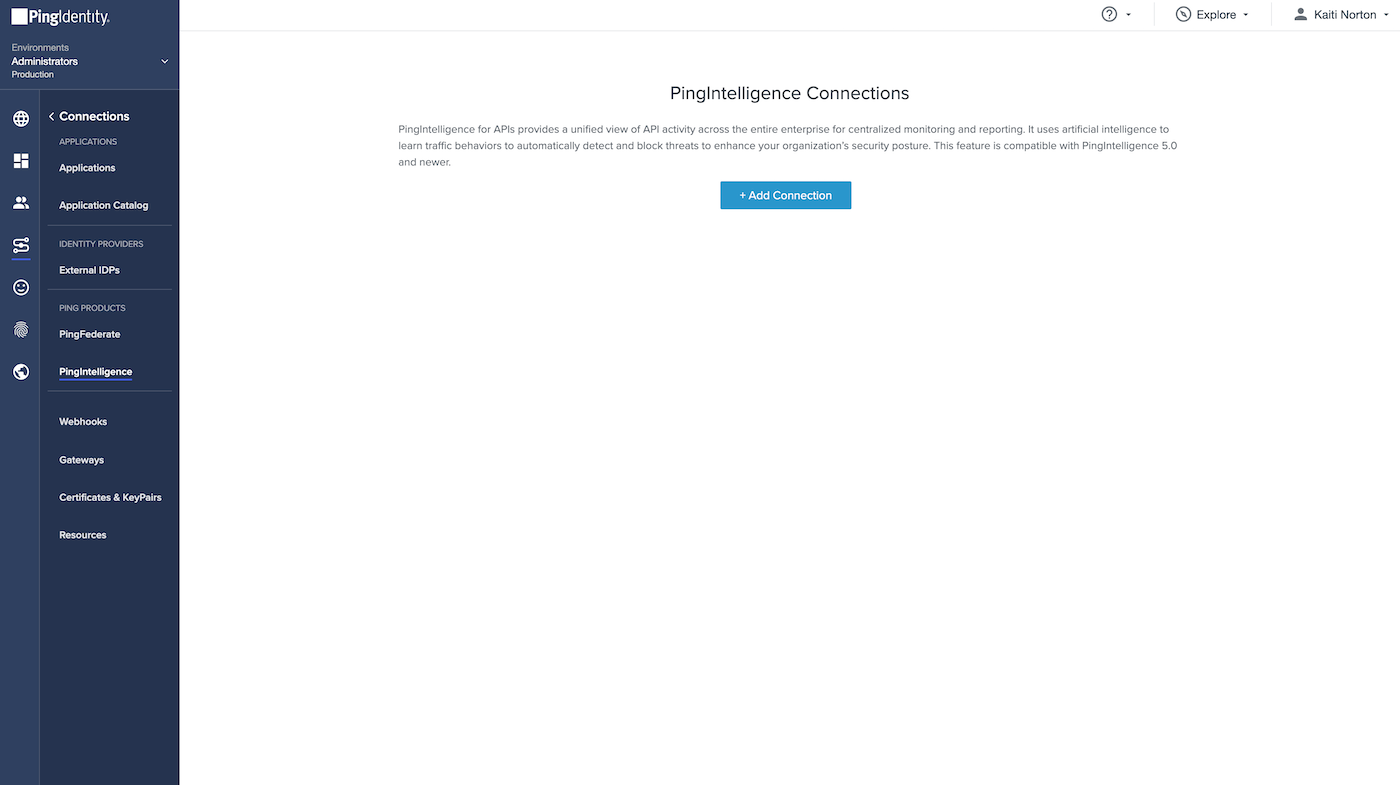
Last but certainly not least, Ping Identity offers multiple monitoring features including risk management, API security, fraud detection, and orchestration. All of these tools work together to keep a constant watchful eye on the system’s risk signals from top to bottom. In the long run, these help create a frictionless user experience and a proactive security framework without creating more work for your IT staff.
Ping Identity Pricing
Ping Identity does not provide pricing for its software upfront. Instead, the Ping sales team creates custom packages based on each customer’s unique needs for customer and workforce identity access management. Ping does provide access to a free trial without requiring any credit card details, so it’s an easy way to get a first-hand look at the platform without needing to speak to a sales rep first.
How to Choose the Best IAM Software
There are many IAM software vendors that suit a variety of different needs. If you’re looking for a solution that can help you manage your customer or employees identity data with cutting-edge authentication features, Ping Identity might be the best fit for you. If you’re still exploring your options, however, our list of the Best IAM Solutions & Tools may be able to help.


