Held in Las Vegas annually, the Consumer Electronics Show (CES) stands as a symbol of what is possible in technology. CES has served as the proving ground for innovators and breakthrough technologies for more than 40 years — a global stage where next-generation innovations are introduced to the marketplace. And 2015’s show was no exception.
Networked homes, more capable wearable devices, wireless entertainment and even your own personal drones were at the head of the list for 2015. While the tech geek is busting at the seams with anticipation, the network administrator is scared to death. All of this technology results in bandwidth hoarding, security vulnerabilities and compliance concerns for IT departments.
In this slideshow, Ipswitch, a software and service provider, explores the technologies emerging from CES with the most potential to disrupt the business and network. If you’re a network administrator, these six trends should have you concerned.
Six Trends Disrupting the Network
Click through for six technology trends emerging from CES 2015 with the most potential to disrupt the business and network, as identified by Ipswitch.
The Wearable Watch – Data Control
The wearable watch will be a major trend in 2015 with the highly anticipated launch of the Apple Watch and a number of other popular watches already on the market. Samsung introduced its Gear S at CES, which is essentially a phone for your wrist. It includes a SIM card, makes calls and accesses the Internet. With the Gear S, Samsung makes one of the boldest plays, suggesting consumers replace phones entirely. Similar devices, including Withings Activité Pop, Garmin Fenix 3, LG Audi smartwatch and Guess Connect, encourage consumers to stay connected through all hours of the day. As employees introduce these connected devices alongside smartphones and tablets to the network, the level of data control that IT has diminishes. Overall, the watch is trending to be one of the biggest IT headaches this year.
Intel Curie – Shadow IT
Intel’s Curie highlighted the new reality that big concerns can come in small packages, or button-sized computers, as they describe their new technology scheduled to debut in the second half of 2015. Why is this a big concern? The technology that typically wreaks the most havoc for IT is the technology IT doesn’t know about. As the gadgets continue to get smaller yet more powerful, IT is caught in a perpetual game of catchup, trying to deal with the new demands on the network by seemingly undetectable technology.
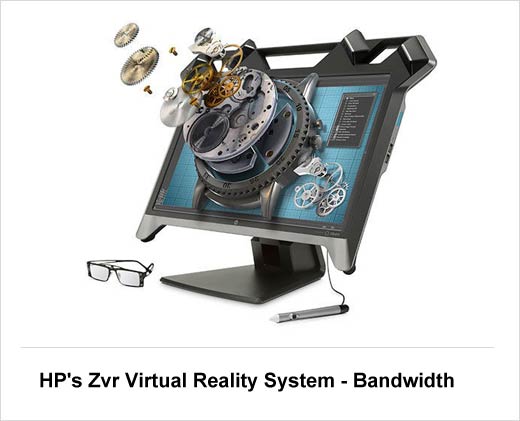
HP’s Zvr Virtual Reality System – Bandwidth
While users will undoubtedly look at systems such as the new HP Zvr and say “cool,” network managers will scream bandwidth limitations. HP states that “users interact seamlessly with a high-definition 3D stereoscopic display combined with full-motion parallax and direct interaction, delivering an intuitive user experience with lifelike realism.” Something tells us that this technology trend makes the bandwidth issue of employees watching YouTube at work the least of IT’s problem. The trend of high-production, high-bandwidth usage technologies taking over the workplace is a very real possibility in coming years.
Sony NW-ZX2 Hi-Res Walkman – Wi-Fi Strength
While the term Walkman may make you think of a dated technology, the newest addition to the Sony Walkman lineup not only can play nearly any audio format, it comes fully equipped with Wi-Fi capability, representing yet another form of technology set to invade the corporate arena. Wireless audio is a trend that should have network administrators concerned as these aren’t the simple speakers of yesterday, but powerful devices capable of severely draining the Wi-Fi strength within the organization.
Fitbit Charge HR – Increased Vulnerabilities
Technology such as the new heart-rate monitoring version of Fitbit’s fitness tracker is making the world smarter about fitness. But what does that mean for the health of your corporate network? More employee-controlled devices with the ability to connect to the network mean more points of vulnerability and bandwidth usage. While on their own, the impact is relatively small, the combined impact of these increasingly popular and affordable devices can create an impact on the enterprise. And as technology has proven over and over again, while it may start small, its impact only increases over time, creating numerous points of access and vulnerability.
Wocket – Compliance
Is the smart wallet a dumb idea for corporate IT? What some are dubbing the “Costanza,” the Wocket replaces all your credit cards with a single, all-purpose smart card. While it represents a breakthrough in consumer technology, it is also another personal technology that employees will integrate into corporate networks. As this trend continues to become more prolific, IT may have to begin seriously drawing the line on which types of consumer technology can and cannot access the organizations network. Technologies such as these can run the risk of customer data ending up in the wrong places on the wrong device, creating the potential for non-compliance.