One of the challenges any IT organization faces when managing endpoints is that end users turn those devices on and off whenever it suits them. To provide a level of persistence across the applications running on those endpoints, Absolute Software developed agent software designed to make it simpler to enable applications to self-heal. Absolute Software today announced it is extending that capability to remediate application issues by accessing current patch and version profiles via Reach technology that is being included in version 7 of the company’s namesake security software.
Jason Short, senior director of product management for Absolute Software, says the Reach technology developed by Absolute leverages the application persistence provided by Absolute to enable IT administrators to deliver patches and updates or other code delivered via a scripting language to applications without waiting for them to be physically connected to the network. Those patches and updates are automatically delivered the next time the end user turns their device on and connects to a network.
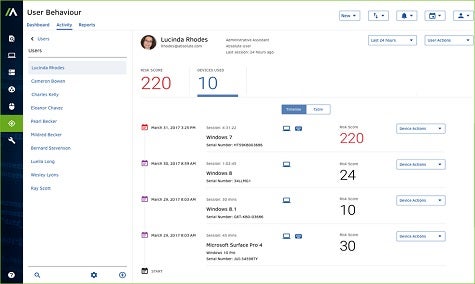
“We’re giving IT organizations full visibility and control,” says Short.
Short says Absolute Software is developing a library of custom and verified scripts that can be employed to deliver the right patch to a specific device automatically. That approach not only eliminates many of the routine tasks associated with patch management, it also eliminates the need for dedicated patch management tools, says Short.
Absolute Software is also exposing an application programming interface (API) through which third-party management applications will be able to collect, for example, endpoint inventory data collected by the agent software deployed by Absolute.
Ever since the rise of mobile computing, the management of endpoints attached to a network has been a major challenge. End users don’t much care where they access a wireless network, which means mobile devices are frequently loaded with malware that can easily be distributed across the enterprise once a mobile device connects to a corporate network. There’s not much that can be done to prevent end users from engaging in the behavior. But at the very least, it’s now possible for IT organizations to first remediate malware issues in addition to hopefully eliminating the vulnerabilities that malware is trying to exploit in the first place.