While insider attacks tend to generate a lot of attention, the number of times that an employee actually goes rogue is fairly low compared to all the other types of security attacks launched at enterprises daily. What is more common is for the credentials of an employee to be compromised, which often has the same profile as an insider attack.
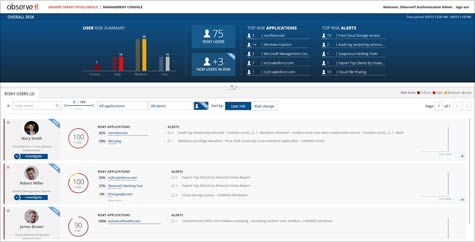
Attacks using social engineering techniques or simply because the passwords in place were too weak lead to compromised accounts within the enterprise. And once an account has been hacked, all the traditional IT security technologies in the world are not going to do much to prevent the attacker from gaining entrance. To help organizations better identify when those credentials have been compromised, ObserveIT has released the version 6.0 upgrade to its namesake platform for tracking end-user behavior that now includes the User Risk Dashboard.
ObserveIT CEO Paul Brady says that depending on log data to figure out which employee might have gone rogue or had their credentials compromised takes too much time and effort on the part of the IT organization to succeed. ObserveIT 6.0 enables organizations to attach a mark to the company’s most sensitive data using agent software and then track who is accessing it. Any anomalies in terms of how that data is being accessed, such as an odd location or time, are immediate flagged. That approach, says Brady, makes it simpler for IT organizations to not only track activity surrounding their highest risk employees, but it also creates an audit trail that IT organizations can use to meet any compliance requirement.
While there will never be perfect security, organizations can protect themselves simply by focusing on things like employee training. But to complement those efforts, organizations also need to be able to identify atypical end-user behaviors.
Using ObserveIT 6.0. may detect something as routine as employees deciding to work with a set of data offline on their own personal device, but it could also discover a major security breach involving thousands of customer records. In either case, the number-one priority is to first identify the behavior, and then decide whether it is benign or an internal or outside lead attack.