As part of a broader effort to create a new standard that will create an open standard to address strong authentication, Nok Nok Labs today launched a Unified Authentication Infrastructure platform that works with a broad array of existing technologies such as fingerprint sensors or webcams, Trusted Platform Module (TPM) chips, or voice biometrics, to authenticate anyone, anywhere using any device without requiring them to even use a password.
According to Nok Nok Labs CEO Phil Dunkelberger, the Unified Authentication Infrastructure platform is the first instance of an approach to authentication that supports a new open standard that is being put forward by a consortium led by PayPal, Lenovo, Validity, Agnitio and Infineon. Dubbed The FIDO Alliance, the goal is to allow any website or cloud application to interface with a broad variety of existing and future FIDO-enabled devices and technologies that the user has available for online security.
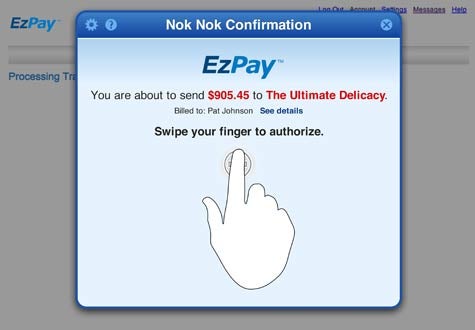
For example, Dunkelberger says a website would be able to automatically discover that a user had a fingerprint reader or TPM chip on their PC to then authenticate a particular user. Or it may rely on a software-only approach that could be driven through an implementation of the standard in the browser, says Dunkelberger. In either instance, the goal is to make the authentication process seamless without having to rely on a service managed by a third-party that adds both cost and latency to a transaction or process.
While FIDO is clearly off to a good start, it will need a lot more backing, particularly among developers of Web applications, to succeed. Dunkelberger says that given all the security issues developers of Web applications now routinely face, it’s clearly time for a more sophisticated approach to authentication. Dunkelberger says he expects to see a broad range of APIs that will make it simpler for developers to take advantage of the FIDO Alliance approach to authentication.
Clearly a big part of the security issue today is that passwords, as evidenced by the most recent breach of Twitter, are not working. They are too easy for hackers to steal, and most end users can only remember a few variants that are usually based on easily identifiable traits such as the name of loved one or a pet dog. What’s needed is an approach to authentication that doesn’t have to be so dependent on how security-conscious the end user actually is.
And, of course, the amount of time and money an organization might save from not having to constantly reset passwords would probably pay for the cost of the effort.