There are ambitious mobile application management platforms (MAM) available. In some cases, this functionality is delivered in standalone MAM platforms. In others, it comes as a module in a broader suite of services. In either case, the tasks MAM performs are vital.
It is easy to get lost in acronyms and details, said Scott Lawrence, the vice president for Performance and Analytics for consulting firm AOTMP, a telecom management and training firm. “First, the platform must be intuitive and easy to use. Enterprises do not have time to figure out how MAM software is supposed to work,” wrote. “Second, and maybe more important, is the service and support provided by the vendor. There is nothing more frustrating to an enterprise when they are unable to resolve their issues or get answers to questions in a timely manner.”
Best Mobile Application Management Tools and Vendors
Pulse Secure’s Workspace
The platform provides simplified, secure access with single sign-on (SSO) and certificate-based authentication offers rapid application access. Applications can be curated by group and can be pushed to users in a mandated fashion or downloaded at their convenience. Device container security for iOS and Android includes encryption of all data, controlled data sharing between apps, on-demand VPN, policy-based split tunneling and enterprise wipe.
ManageEngine Mobile Device Manager Plus
The platform enforces data loss prevention with customizable corporate security policies that secure mobile data when it’s at rest, in use and in transit. It secures sensitive business data, including information that’s stored on misplaced or stolen devices.
The platform combats shadow IT by managing and distributing both in-house and store apps to employee- and corporate-owned devices. It manages app licenses and controls app updates to ensure devices are provisioned with the required apps. It tests, schedules and deploys OS updates based on organizational requirements.
The platform automates device provisioning and access controls by setting up automated enrollment to bring mobile devices under management before unboxing them. Once enrolled, the platform auto-assigns devices to groups based on internal departments. Security policies, access controls, and apps associated with these groups will be automatically applied to these devices.
IBM MaaS360 with Watson
The platform includes a leading container app solution for secure productivity that is deployed in most highly regulated environments. Alongside its container, MaaS360 also offers identity and access management with single sign-on and conditional access capabilities out of the box. With Watson, MaaS360 Advisor provides real-time risk insights and recommended remediation path.
Arxan
The Apperian MAM features private enterprise app stores, secure app distribution and app security and management policies. All are supported by Arxan’s platform-as-a-service offering, which allows for extensibility, automation and customization.
Appaloosa Store
The approach is a native app store with “silent” instance, update, wipe and instant deployment.
SOTI MobiControl
The platform can silently install, update or remove apps on devices based on whether an authorized user of the device has been granted access to the app. It can integrate with the Apple App Store or Google Play Store to deploy apps that have been authorized or purchased by the organization. A third capability is to enforce DLP to disable sharing of data within a managed application to an unmanaged application such as an individual’s personal DropBox account.
Microsoft Intune
Multi-identity, Selective Wipe (available only via iOS and Android platforms). Users can open web links securely through Intune Managed Browser app and app protection policies.
MobileIron
The top features are a rich set of security policies, passwordless authentication, and a robust app discovery experience for the end user.
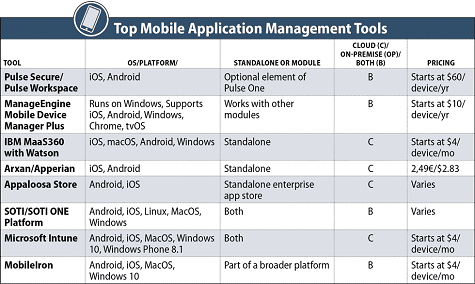
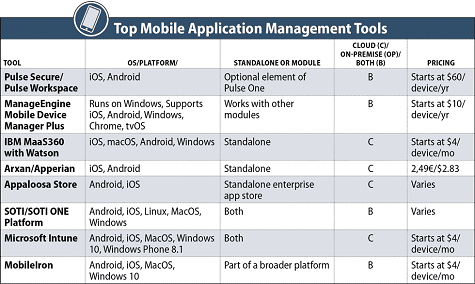
Top Mobile Application Management (MAM) Tool Comparison Chart