The global survey of 384 business managers finds that most think they probably have an issue with security in software-as-a-service (Saas) applications in the cloud, and the vast majority think it will require a collaborative effort to truly make cloud computing secure.
Click through for results from a survey conducted by Courion on cloud computing security.
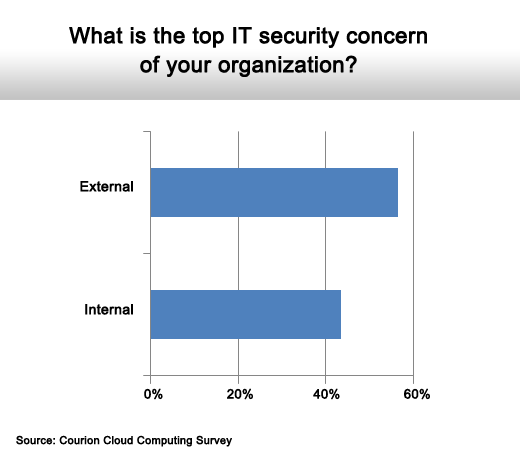
Threats are roughly equally mixed.
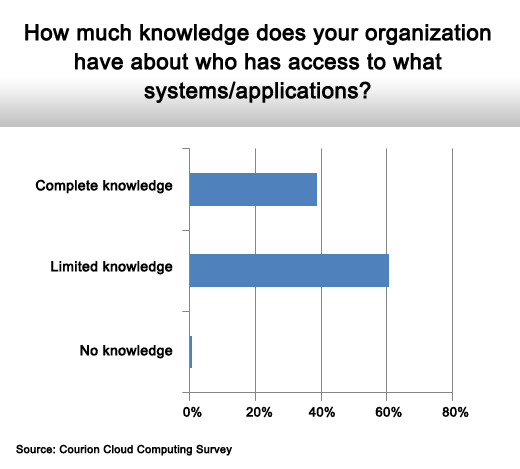
The majority have limited knowledge.
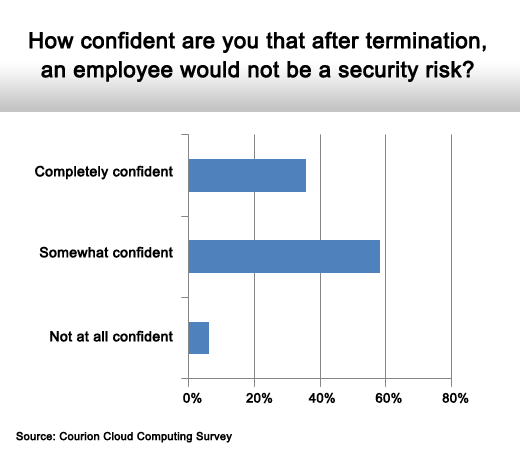
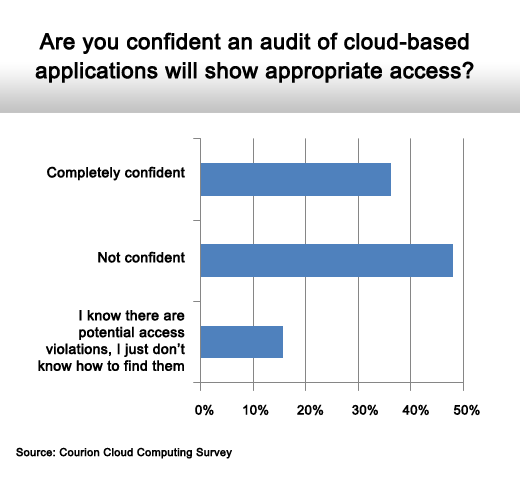
There are lots of doubts.
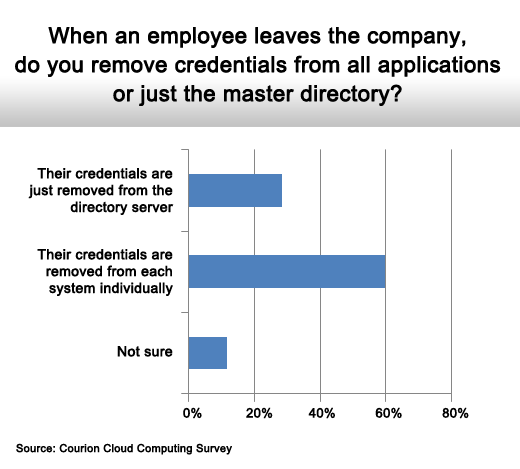
Most remove credentials at application level.
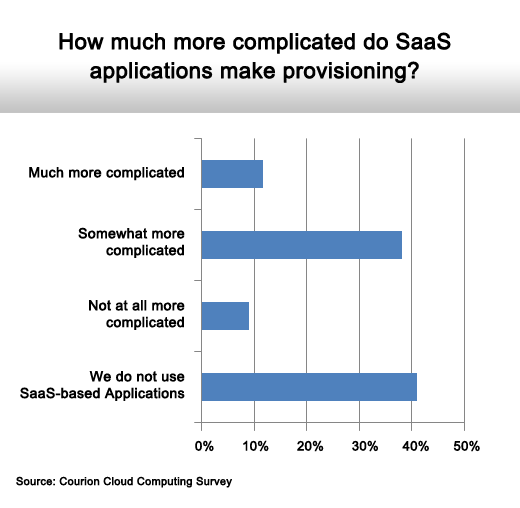
SaaS adds overhead to provision management.
The majority think they probably have an issue.
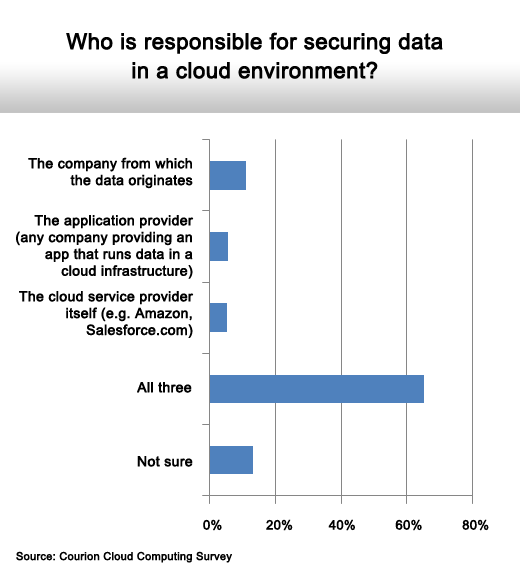
It’s a collaborative effort.