With the network perimeter increasingly becoming too porous to defend, IT organizations have been looking for new ways to defend individual applications and the data they contain. With that goal in mind, Hewlett-Packard today announced HP Application Defender, a software-as-a-service (SaaS) application that centralizes the management of application security via the cloud.
Maria Bledsoe, senior manager for Fortify product marketing within HP Enterprise Security Products, says HP Application Defender allows IT organizations to insert run-time code in their applications that automatically connects that application to the security service provided by HP Application Defender.
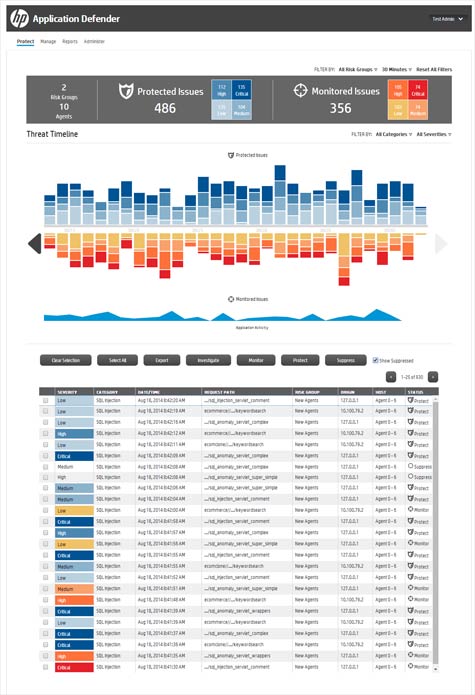
Those security services include everything from analyzing user actions to detecting data anomalies and alterations to logic flow to distinguish between an actual attack and a legitimate user request. Once an issue is discovered, IT organizations can then invoke HP Application Defender dashboards to remedy the exploit.
As part of a new class of Runtime Application Self Protection (RASP) products, Bledsoe says HP Application Defender is designed to shift the focus of IT security to the application rather than solely the network perimeter.
IT security has clearly turned into a game of cat and mouse. The problem is that because IT organizations have little to no visibility when it comes to what is happening inside an application in real time, their ability to proactively respond to potential threats is severely limited. By deploying HP Application Defender, applications can be more readily defended at run-time in a way that doesn’t require developers to alter how their code is developed, says Bledsoe.
In general, too much IT security spending is focused on defending a perimeter that is not only compromised almost by definition; it’s hard to even identify where that perimeter is given the fact that so many applications now run on mobile computing devices. The degree to which RASP represents a more effective approach to IT security remains to be proven. But the one thing that is for certain is that most of the existing IT security measures in place are no longer nearly as effective as they once might have been.