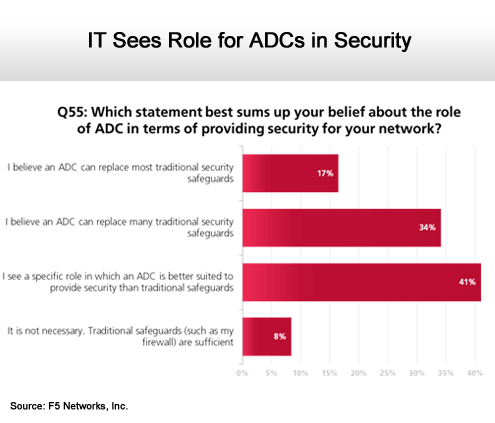
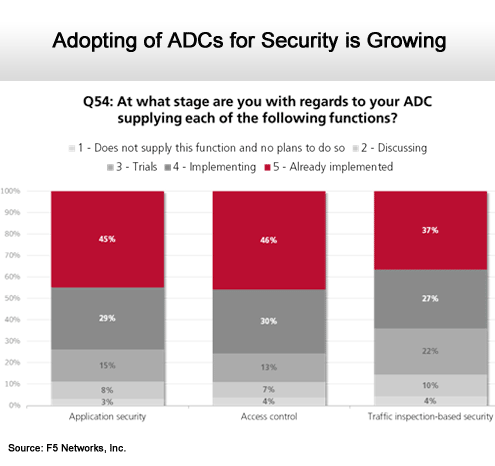
In a worldwide survey conducted by Applied Research on behalf of F5 Networks, about half of the 1,000 large organizations surveyed said they see ADCs as being a platform that could eliminate the need for some security appliances, while one-third said they were already using ADCs in that context.
Obviously, next-generation firewall vendors are making many of the same claims. What appears to be happening is a convergence of functionality at the edge of the network as ADCs evolve into a platform capable of providing multiple services, including security.
Murphy says this approach is going to prove critical over time because existing approaches to network and application security require the deployment of separate layers of security that are generally poorly integrated. Converging those functions around one integrated platform, says Murphy, not only makes economic sense, but it should also lead to better security by making it easier to correlate information across different classes of attacks.
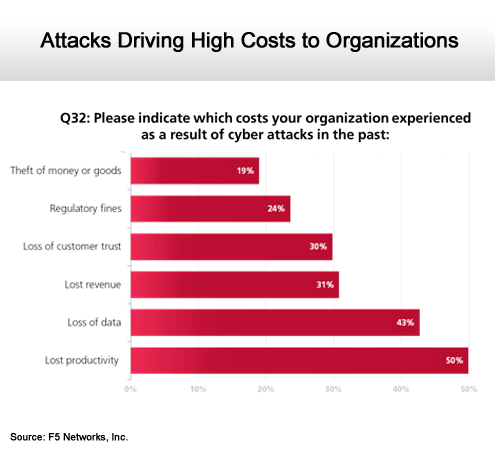
Something is clearly wrong with IT security given the frequency of attacks and the actual amount of real dollars being lost. The challenge facing IT organizations is how to come up with a comprehensive approach to security that makes it easier to first identify those threats and then combat them in a single motion. It’s not quite clear what approach will ultimately provide that capability, but somewhere between the ADC and a next-generation firewall there probably is an answer.
Click through for results from a ADC security survey conducted by F5 Networks, Inc.
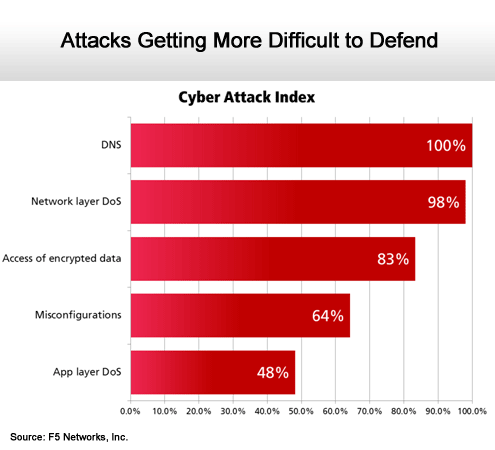
DNS attacks top list of most lethal.
The problem continues to grow.
A convergence of network and application security.
Those that have ADCs understand their value.