While just about every organization deploys antivirus software on endpoints, there’s generally not much faith that the amount of protection being provided makes installing this class of security software worth the effort. In fact, beyond providing protection against the most routine types of attacks, antivirus software is often severely challenged when it comes to defending against modern forms of malware.
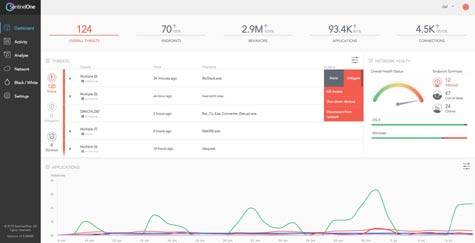
Today, SentinelOne says there is finally a viable alternative that relies on heuristics technology to protect Windows, OS X and Android devices. The SentinelOne EndpointProtection Platform (EPP) makes use of dynamic execution inspection technology to monitor behaviors based on the instrumentation of operating system activities and operations such as memory, disk, registry and network usage.
SentinelOne CEO Tomer Weingarten says that instead of relying on signatures based on types of malware that take time to develop, SentinelOne EPP detects malicious code based on its exploit techniques, including “heap spraying, stack pivots, ROP attacks and memory permission modifications.” That approach is not only more effective, says Weingarten, it is less taxing on the endpoint from a CPU perspective.
While SentinelOne previously monitored endpoints for potential threats, the arrival of SentinelOne EPP means that IT organizations can now replace their AV software altogether, says Weingarten.
In addition to providing the heuristics engine to combat malware, SentinelOne EPP integrates with cloud intelligence and selects reputation services to provide a lightweight method to index files for passive scanning, instead of performing resource-intensive system scans. It includes a policy-based mitigation option that can automatically kill or isolate specific processes in real time.
Should malware ever create, modify or delete system files or registry settings or make changes to configuration settings, SentinelOne EPP can also be used to restore endpoints to their trusted, pre-malware state. SentinelOne also includes an audit trail that enables security professionals to keep track of which actions were taken, when, and for what particular reason.
When it comes to endpoint security, there’s naturally a lot of frustration. Organizations that have hundreds or even thousands of endpoints spend a significant amount of money on AV software that provides only a limited amount of malware protection. While there may never be such a thing as perfect endpoint security, there is clearly a need for an alternative approach to a problem that is getting more pervasive and posing potentially catastrophic results for organizations.