When attackers compromise a business email account, the average total cost of that data breach is $5.01 million. Phishing and social engineering are huge security problems for organizations, and they often struggle to find solutions for them. Cybersecurity company odix removes malicious code from email files and provides a clean copy to the recipient. To provide more insight on how this works, let’s look at global clean-tech company Clariter and how they used odix to protect their corporate email accounts.
The odix approach to malware prevention
- Company overviews: Clariter and odix
- The problem Clariter faces with malware
- FileWall from odix provides the solution
- Protecting your company from emailed malware
Company Overviews: Clariter and odix
Clariter
Clariter is an innovative green technology company that has created a chemical upcycling solution to reduce the life of plastic waste. It helps reduce the amount of plastic that is burned or that ends up in landfills by turning it into useful oils, waxes, and solvents, which it then sells to companies to use in products like candles, car wax, and furniture polish.
By using plastic waste as the basis for these products, Clariter provides a more sustainable, eco-friendly option than the petrochemicals many businesses currently use. Not only does this lower the amount of plastic waste, but it also reduces dependence on crude oil.
odix
Led by the former head of the Israeli defense force’s cyber defense unit, odix is a content disarm and reconstruction (CDR) technology company that helps protect businesses from malware. Its platform works with both known and unknown malware for more thorough security.
odix scans and removes malware from a variety of file locations, including email, USB drives, and transferred files. Then, it provides a clean copy of the file to the user, helping to create an extra layer of security between a company’s employees and bad actors.
The Problem Clariter Faces with Malware
Clariter has nearly 100 employees and expects to add more this year. With that many email accounts, it’s a prime target for phishing attempts. Additionally, Clariter uses Microsoft Exchange for their email server, and research from Check Point shows that Microsoft is the most common brand that attackers attempt to impersonate when they send phishing emails. With all that in mind, the organization needed to add extra protection to their employees’ email accounts.
Lance Soller, the group IT manager for Clariter says, “With our team spread out across multiple locations worldwide, we need to be able to securely share data and protect our team and assets from cyberattacks.”
The Solution: FileWall from odix
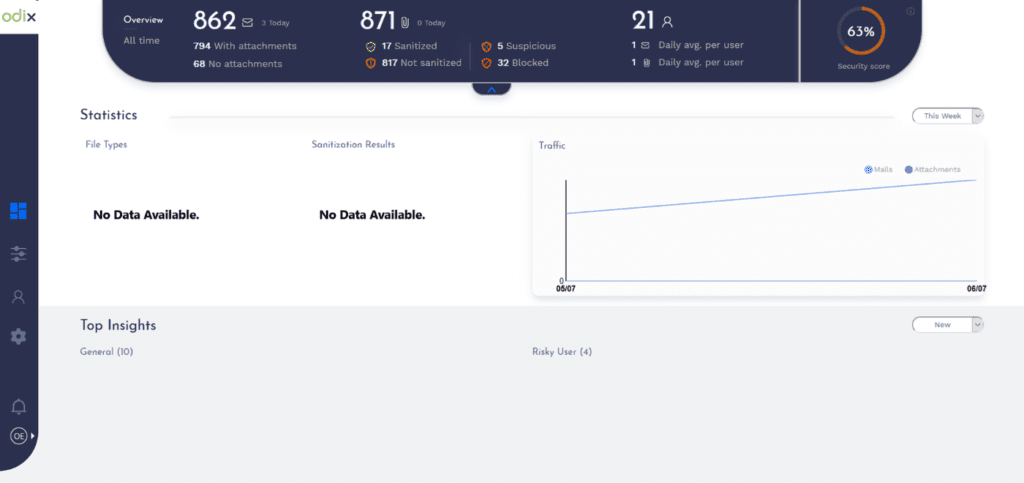
FileWall from odix was specifically designed to protect Microsoft 365 users from malware threats. It works as a plug-in for Microsoft 365 inboxes, removing attachment-based threats from emails, cleaning the files, and providing clean versions to the recipient.

Soller says odix has given them a way to share data securely and keep their employees safe from phishing attacks. “FileWall gives us unmatched malware protection and perfectly complements our Microsoft 365 deployment.” FileWall also works with Microsoft Defender to keep any threats from slipping through the cracks.
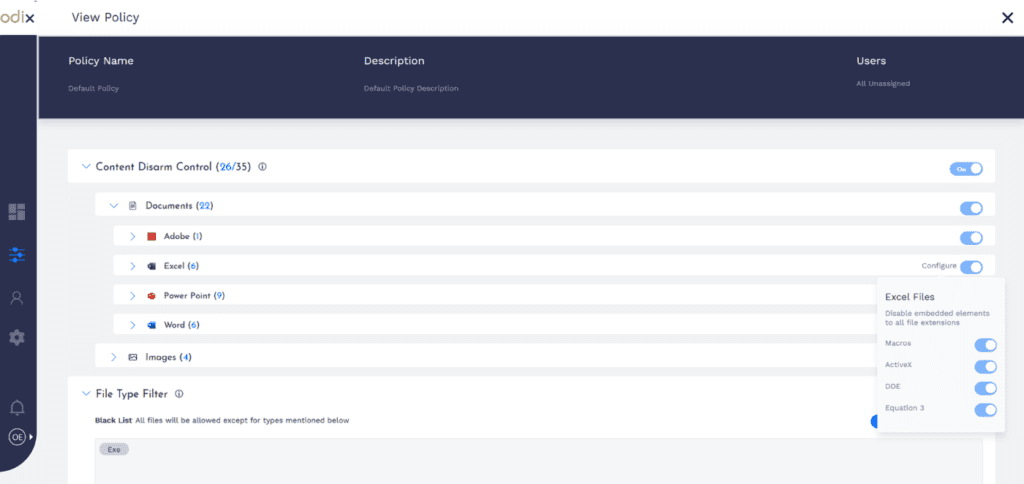
Despite cybersecurity training, 34 percent of cyberattacks involve internal employees. However, odix reduces this number by removing the threat from emails. Even if an employee opens an attachment from an unknown sender, it’ll be a clean version, thanks to the CDR technology.
Protecting Your Company From Emailed Malware
Phishing and email malware continue to be major threats for enterprises. Along with adding security tools to their network, like odix or an endpoint protection platform, organizations need to provide their employees with thorough training on phishing attacks. Employees need to know what to look out for and what they should do if they suspect they’ve fallen victim to a phishing attempt.
Organizations need to refrain from shaming employees if they do make a mistake. It doesn’t solve the issue, and they’ll be less likely to report it if it happens again, leaving the business vulnerable.
Read next: Email Security Tips to Prevent Phishing and Malware


