There’s a lot of discussion in IT circles about how to best go about managing identity that usually results in a lot of frustration. There’s not much in the way of actual standards when it comes to identity management, so it’s not uncommon to see IT organizations that embark on trying to solve this problem spending hundreds of thousands of dollars with little to show for their efforts.
Rather than thinking of identity management as a problem that needs to be solved by IT, providers of managed services such as N8 Identity are making the case that identity management should really be a natural extension of the processes that already exist in the human resources department. After all, just about anybody who has anything to do with the company at some point winds up touching at least one HR process.
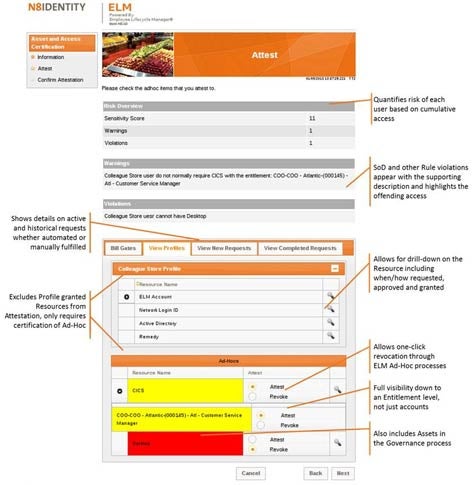
With that thought in mind, N8 Identity created a managed service for managing identities that is based on a suite of applications the company developed for HR professionals. That service can then be used to provision who should have access to what applications using what devices based on their role in the organization. For IT to develop the equivalent of such an application, the costs easily spiral out of control because for the most part IT is working with a raw set of identity management technologies that generally require expensive consultants to craft into an actual application.
N8 Identity CEO Jay O’Donnell says that after building a few of these applications, it became apparent to N8 Identity that creating an employee lifecycle application for HR departments that was delivered as a managed service would be a much more efficient route to manage identities, especially when you consider the fact that it’s usually someone outside of IT that needs to decide who should have access to what resources within the organization.
IT departments have been drawn into identity management projects that involve writing custom code with predictable results for more years than anyone cares to remember. The question that needs to be asked now is whether identity management is the best use of limited internal IT resources or has the time come to rely on an actual application that not only is specifically designed to address the issues involved, but also requires little to no IT intervention to actually be deployed.