Hackers are sometimes used as consultants to help companies improve their digital security. Referred to as ethical hackers, they use hacking software to test your systems to see if they’re vulnerable before an attacker does it for you.
Table of Contents
What is Ethical Hacking?
Hacking is the use of any tools or technology to obtain unauthorized access to or circumvent security measures of a computer system or network.
An ethical hacker is an independent security tester who checks computer systems, networks, and programs, looking for potential vulnerabilities that an attacker could exploit. Ethical hackers use the same tools and techniques as malicious hackers; however, they do it to improve system security and uphold privacy policies and standards instead of causing damage or stealing information. Examples include penetration testing and vulnerability scanning.
Companies often hire ethical hackers to perform penetration tests in order to find vulnerabilities that cybercriminals could exploit in an attack. These are also known as black-box tests because they involve using automated tools without knowing how systems are configured or what vulnerabilities may exist. The goal is to simulate real-world attacks so that companies can identify and fix weaknesses before cybercriminals exploit them.
Also read: Best Vulnerability Management Tools 2022
What are Hacking Tools?
In computer security, a hacking tool is designed to help hackers gain unauthorized access to information. The term usually refers to general-purpose tools used in many types of attacks rather than custom-made exploits for specific systems. Most hacking tools are either open source or freeware/shareware, making them easily accessible for anyone who wishes to use them for malicious purposes.
Security professionals use ethical hacking tools to assess vulnerabilities in computer systems to improve their security. These tools include packet sniffers for intercepting network traffic, password crackers for discovering passwords, and port scanners for identifying open ports on computers.
The field of network administration has grown from simple monitoring of networks to actively managing them through firewalls, VPNs, intrusion detection systems (IDS), anti-virus software, anti-spam filters and other technology.
Also read: Best Patch Management Software Solutions 2022
Why is Hacking Software Important?
Most people think of hacking in a negative light—there’s no denying that some hackers cause damage. But in reality, most ethical hackers are hired to protect valuable assets like data, software, and hardware. These professionals use specialized tools to find vulnerabilities in systems before malicious parties can take advantage of them. These hacking tools help ensure that security doesn’t become an afterthought but rather a necessity throughout every stage of development. They also ensure that end users are protected from both inside and outside threats.
Benefits of Ethical Hacking Tools
Enterprise uses ethical hacking tools to test their internet security, secure their network or office system, audit their company’s security or assess if a system is vulnerable to attacks. Other benefits include:
- They help you test your network security and find any loopholes in it to fix them before an attacker takes advantage of them.
- When securing your home network, there are several ethical hacking tools available online that you can download for free and use to keep yourself safe from cyber threats.
- They will help you audit your company’s security and ensure everything is running smoothly without any issues.
- If you want to know how vulnerable your computer or network is to external attacks, they allow you to do vulnerability assessments on your system.
- They help penetration testers with their work because penetration testing involves trying to hack into someone else’s system.
Top 8 Best Hacking Tools and Software
Whether you’re an IT expert or an ethical hacker, it’s important to have the right tools. There are many different computer and network hacking tools available today, so choosing which ones can be difficult. To help you make a more informed decision about which tools to purchase, we’ve put together a list of our top eight picks to help you decide on the best option.
Invicti
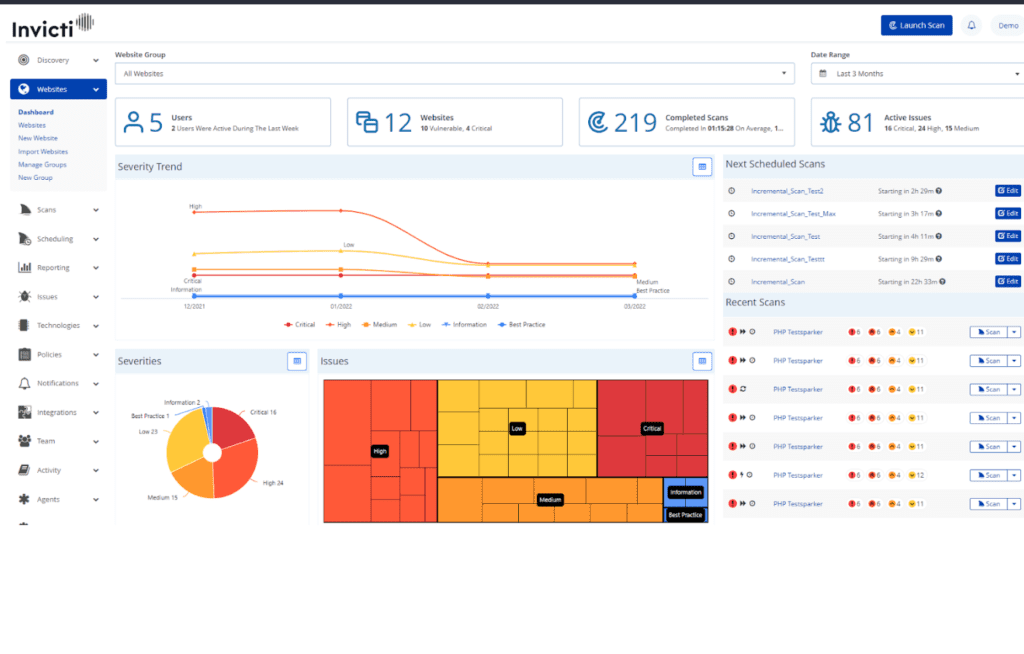
Invicti (formerly Netsparker) is an automated and fully configurable web application security scanner that allows you to scan and discover security problems in websites, web apps, and web services. Invicti can scan different web apps, irrespective of the platform or language used to create them. It also provides proof of the vulnerability, so you don’t have to verify it manually. Invicti enables enterprises with complex environments to automate their web security by providing security teams with the most distinctive DAST + IAST scanning capabilities.
Key Differentiators
- Invicti performs high-precision web application security scans that are not false positives.
- Invicti proof-based scanning tool actively and automatically verifies detected vulnerabilities by exploiting them read-only and secure.
- Invicti lets you use scan policies to define your scan’s type, range, and targets.
- Scans may be started immediately or scheduled for later, including regular intervals.
- Vulnerability management systems, issue tracking systems, continuous integration systems, single sign-on providers, team messaging systems, and web application firewalls are all supported by Invicti.
Pricing: Contact Invicti for pricing quotes tailored to your needs or book a demo before making a purchase decision.
Metasploit Framework
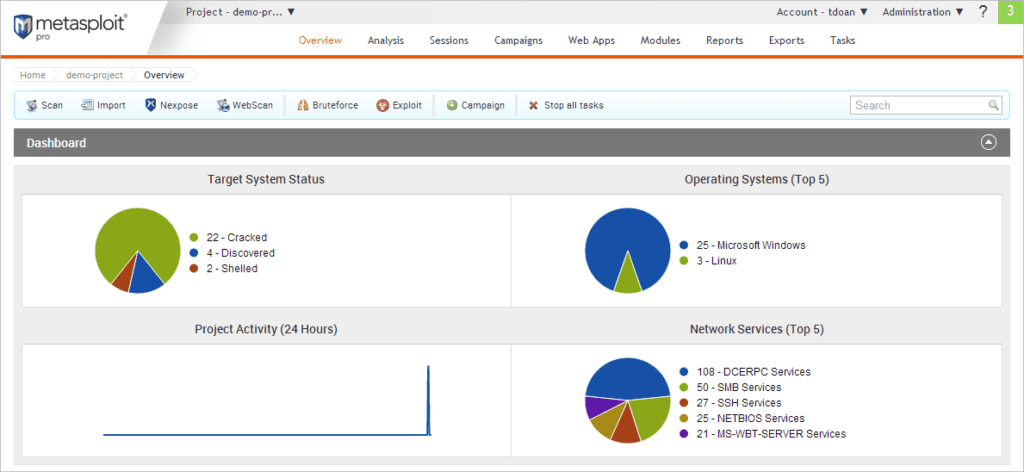
Metasploit is an open-source software framework used to develop, test, and exploit code. This toolkit can aid penetration testers in identifying system vulnerabilities. Developed by HD Moore in 2003, it was acquired by Rapid7 in 2009. It provides information about security vulnerabilities and aids in penetration testing and IDS signature development.
Key Differentiators
- The Metasploit framework discovery scan includes a UDP scan by default, which sends UDP probes to the most frequently used UDP ports, such as NETBIOS, DHCP, DNS, and SNMP.
- Metasploit framework scan analyzes around 250 ports that are regularly accessible for external services and are more frequently examined during a penetration test.
- Metasploit provides exploits, payloads, auxiliary functions, encoders, listeners, shellcode, post-exploitation code and nops.
- Metasploit supports several third-party vulnerability scanners, including Nessus, Qualys, and Core Impact.
- Metasploit auto-exploitation functionality analyzes open services, vulnerability references, and fingerprints for exploits. All matched exploits are put into an attack plan, effectively listing all possible exploits.
Pricing: Metasploit community edition is free. Contact sales for quotes or download the Metasploit framework tool free trial for the pro version.
Burp Suite
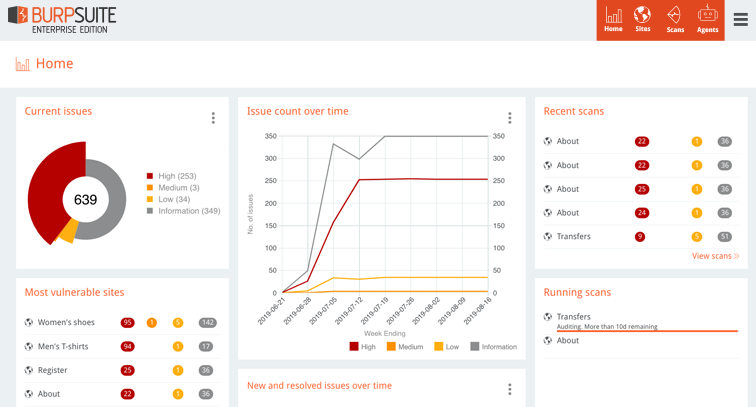
Burp Suite is an integrated platform for performing security testing of web applications. It comprises various tools written in Java, such as an intercepting proxy, a repeater, a sequencer, and a spider tool. All these can be launched within a single graphical user interface (GUI). Using these features of the Burp Suite, you can find vulnerabilities within websites like SQL Injection, etc. Burp Suite helps identify the vulnerabilities and verify the attack vectors with its various features.
Key Differentiators
- Burp Suite’s out-of-band (OAST) capabilities can be used to test for out-of-band vulnerabilities by using a dedicated client manually.
- Burp Suite uses target site maps to gather and store all target data, which may then be filtered and annotated.
- Within a single window, you can modify and reissue individual HTTP and WebSocket messages and evaluate the response.
- Burp Suite determines the size of your intended application; URL parameters and static as well as dynamic URLs are automatically enumerated.
- Burp Suite provides you with WebSockets communications history, which you can see and modify.
Pricing: Burp Suite offers a 30-days free trial for prospective buyers, and the pro version starts at $399.00 per user per month.
Nessus
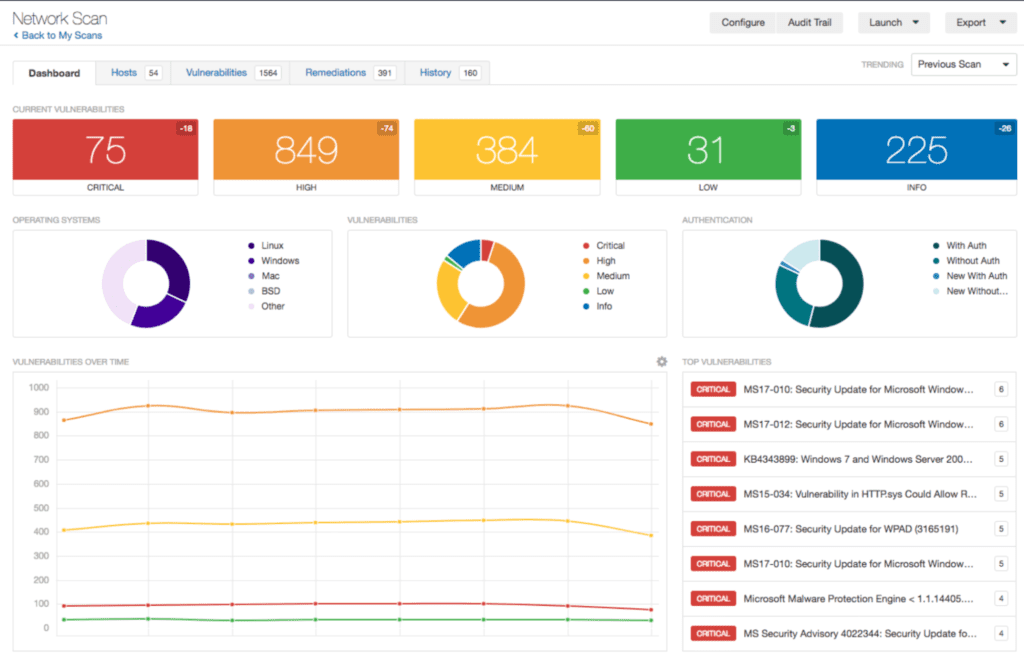
Nessus is a proprietary vulnerability scanner created by Tenable Network Security. This tool is capable of performing in-depth scans for known vulnerabilities as well as detecting any misconfigurations that could potentially lead to security issues. The tool also has an integrated IDS (Intrusion Detection System) engine that can detect network-based attacks. Nessus can be installed on Windows, Linux, OS X, Solaris, HP-UX, AIX, FreeBSD and more.
Key Differentiators
- Botnet/malicious, process/anti-virus auditing.
- Nessus conducts sensitive content auditing such as PII (e.g., credit card numbers, social security numbers, etc.)
- Nessus helps in the implementation of PCI DSS requirements for secure configuration, system hardening, malware detection, web application scanning, and access controls.
- Nessus provides comprehensive vulnerability coverage for virtualization and cloud, malware and botnets, configuration auditing, and web applications.
Pricing: Nessus offers three pricing plans. They include Nessus essential which is free to download, Nessus professional and tenable.io. See breakdown below.
| Nessus professional | Tenable.io (65 assets) | Tenable.io for web scraping (5 FQDNs) |
| 1 Year License – $3,644.25* | 1 Year–$2,934.75 | $3,846.35 |
| 2 Years –$7,106.29* | 2 Years–$5,722.76 | |
| 3 Years – $10,386.11 | 3 Years–$8,364.04 |
Network Mapper (Nmap)
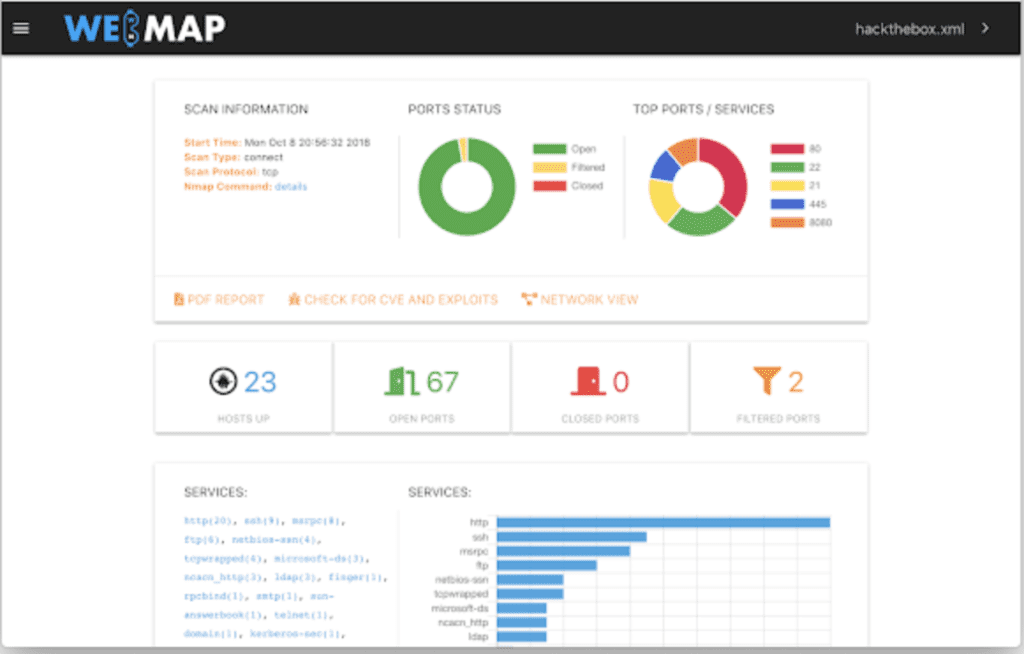
Nmap (Network Mapper) is a free network discovery and security auditing tool. It’s also useful for network inventory, managing service update schedules, and monitoring host or service uptime. For example, Nmap can detect what hosts are present on the network, what services (application name and version) they provide, what operating systems (and OS versions) they run, what packet filters/firewalls they use, and more. It is built to scan large networks and quickly works well on single hosts.
Nmap is available for Linux, Windows, and Mac OS X. The Nmap suite includes a comprehensive GUI and results viewer (Zenmap), a versatile data transfer, redirection, and debugging tool (Ncat), a tool for comparing scan results (Ndiff), and a tool for packet production, and response analysis (Nping).
Key Differentiators
- Nmap supports most operating systems, including Linux, Microsoft Windows, FreeBSD, OpenBSD, Solaris, IRIX, Mac OS X, HP-UX, NetBSD, Sun OS, Amiga, and more.
- Supports dozens of advanced techniques for mapping out densely packed networks with IP filters, firewalls, routers, and other impediments. Other port scanning mechanisms (TCP and UDP), OS detection, version detection, and ping sweeps are also included.
- Generates traffic to hosts on a network, response analysis and response time measurement.
Pricing: Nmap offers several pricing plans for companies of various sizes. They include:
| Plan | Pricing |
| Nmap OEM Enterprise Redistribution License | The perpetual license costs $57,900 with an optional annual maintenance fee of $17,380 |
| Nmap OEM Mid-Sized Company Redistribution License | The perpetual license costs $47,900, plus an optional annual maintenance fee of $14,380 |
| Nmap OEM Small/Startup Company Redistribution License | The perpetual license costs $37,900, plus an optional annual maintenance fee of $11,980 |
Wireshark
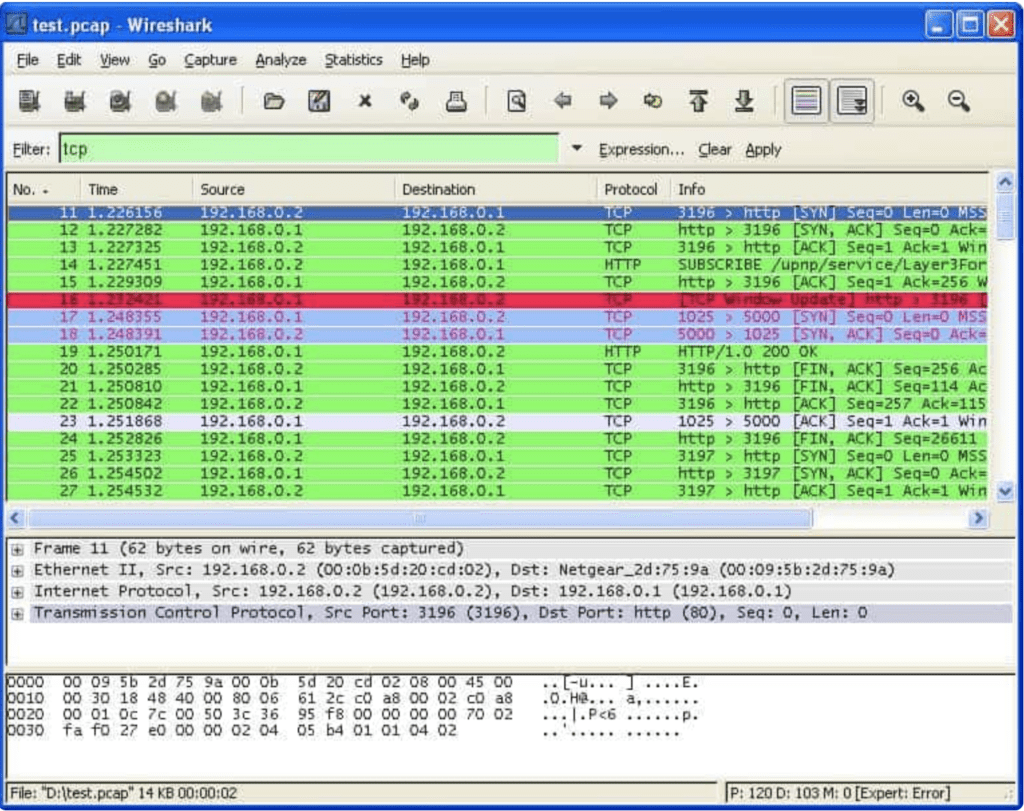
Wireshark is a free and open-source network protocol analyzer and a network sniffer. It is used for network troubleshooting, analysis, software and communications protocol development, and education. Wireshark can also perform live capturing of packets and analyze them on the spot. The user interface is based on GTK+, using libpcap to capture packets from various network interfaces and then display them in a human-readable format.
Key Differentiators
- Live capture and offline analysis.
- Wireshark offers decryption support for many protocols, including IPsec, ISAKMP, Kerberos, SNMPv3, SSL/TLS, WEP, and WPA/WPA2.
- Wireshark captured network data can be browsed through a GUI or the TTY-mode TShark utility.
- Wireshark allows you to see network activity at the most basic level, including PCAP file access, customized reports, and alerts.
Pricing: Wireshark is a free, open-source software application available under the GNU General Public License version.
OpenVAS
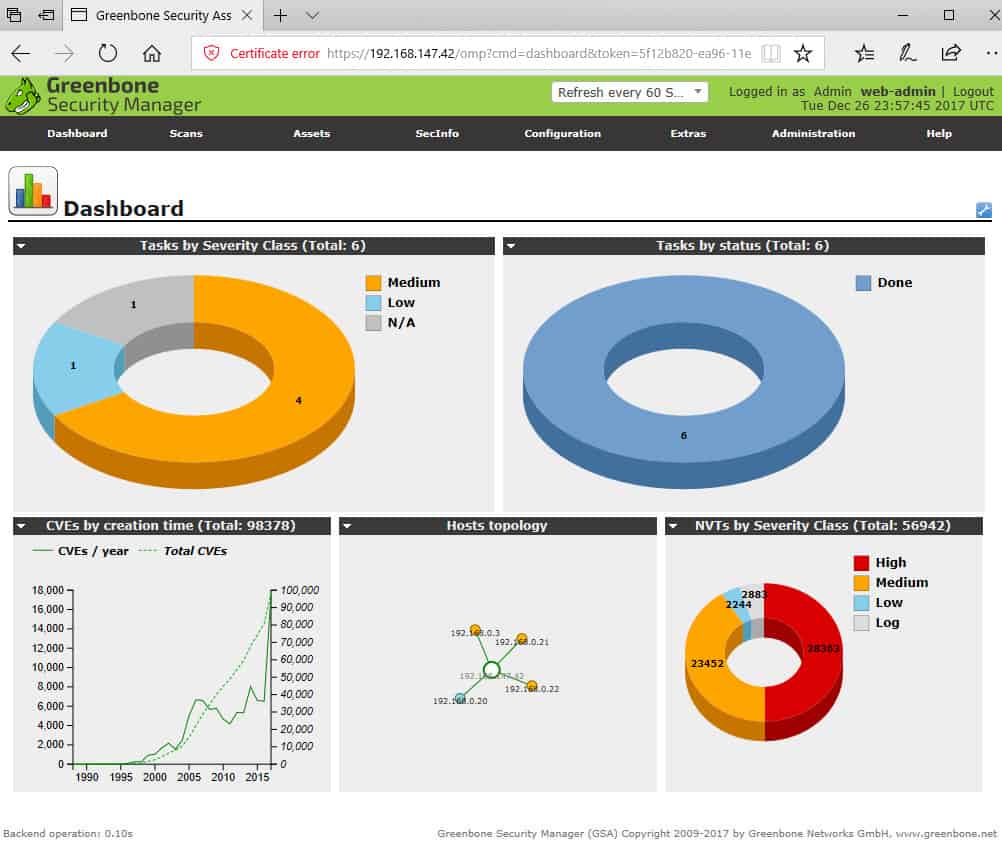
OpenVAS is a comprehensive vulnerability scanner for unauthenticated and authenticated testing, numerous high-level and low-level internet and industrial protocols, performance optimization for large-scale scanning, and a strong internal programming language to execute any vulnerability test.
The scanner obtains vulnerability detection tests from a feed with a long history and regular updates. Greenbone Networks has been developing and advancing OpenVAS since 2006.
Key Differentiators
- Can conduct various sorts of authenticated/unauthenticated tests
- Supports a vast number of internet and industrial protocols, both high- and low-level.
- Has a built-in programming language for developing customized vulnerability testing.
Pricing: OpenVAS is a free tool.
SQLmap
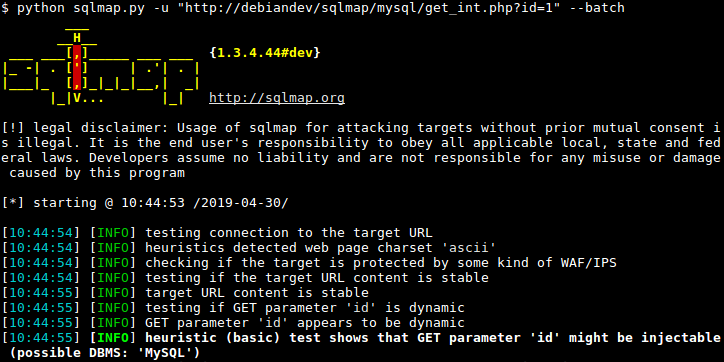
SQLmap is a fully automated SQL injection and database takeover tool preloaded with a wordlist of common SQL syntax error messages. In addition to using that list, SQLmap has an advanced algorithmic engine to guess what injections are valid intelligently. This means you can quickly skip testing injection points where the syntax isn’t right without having to write custom wordlists.
Key Differentiators
- SQLmap can automatically recognize password hash formats and support cracking them using a dictionary-based attack.
- Using MySQL, PostgreSQL, or Microsoft SQL Server, you can download and upload any file from the database server’s underlying file system.
- SQL injection methods are fully supported, including boolean-based blind, time-based blind, error-based, UNION query-based, stacked queries, and out-of-band.
- Capability for establishing an out-of-band stateful TCP connection between the attacker machine and the underlying operating system of the database server.
- Support for enumerating users, password hashes, privileges, roles, databases, tables, and columns.
Pricing: This tool is freely available to download.
Choosing the Best Ethical Hacker Tool
The best ethical hacking tools are constantly being improved by their creators, who continuously add new features and eliminate old bugs. As you’re searching for one, there are some features you need to keep an eye out for including ease of use, a strong user community, and usability on familiar operating systems (Windows, Mac OS X, Linux); most ethical hacking tools work across multiple platforms, but not all do. That said, you shouldn’t have much trouble finding a great ethical hacking tool that suits your needs. Many of them are free or come with trial versions, so you can try them before buying.
Read next: Best Managed Security Service Providers (MSSPs) 2022


