Many IT organizations now routinely contract IT security researchers to ascertain just how secure the software they deploy really is. To facilitate that process, Bugcrowd developed a crowd-sourcing platform, dubbed Crowdcontrol, through which IT organizations can contract security researchers that have been vetted. BugCrowd today announced it is extending Crowdcontrol by adding a Traffic Control capability that makes it possible for penetration testing to be conduced over a virtual private network (VPN).
Jonathan Cran, vice president of product for Bugcrowd, says Crowdcontrol simplifies vulnerability discovery by providing IT organizations with access to a wide variety of professional penetration experts. The issue that many organizations have when using such as a service is that that they can’t expose their applications using public internet connections because of compliance issues. Traffic Control solves that issue by making sure penetration testing is conducted over a VPN, says Cran.
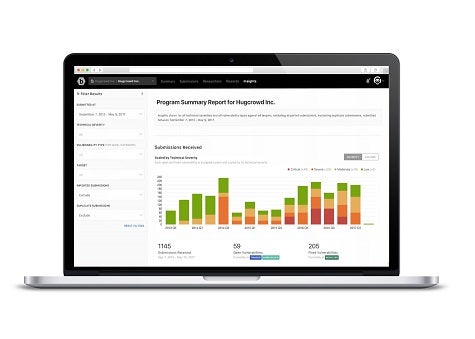
Cran says Traffic Control also provides IT organizations more visibility into which security researcher is accessing what code. In addition, a set of reporting tools make it simpler to track vulnerabilities, says Cran. Those tools are important because IT organizations are now required to demonstrate penetration testing was conducted to comply with various regulations, adds Cran.
In general, Cran says, penetration testing conducted by third-party researchers usually leads to vulnerabilities being discovered that many software engineering teams overlook or discount.
“It can be quite an eye-opening experience,” says Cran. “A lot of researchers can do things in a few minutes that engineering teams think would be unlikely.”
Cran says the good news is that once a third-party researcher discovers a vulnerability, the engineering teams generally pay a lot more attention to security issues.
Penetration testing is often deemed to be a routine exercise by many developers. But as cybercriminals continue to make use of advanced analytics to discover software vulnerabilities, it may turn out that penetration testing is now the first and best line of defense any IT organization can employ.