IT security is almost by definition a team sport. In order to win, IT security analysts need to collaborate. The only way to effectively sort through and prioritize potential threats is to enable as much collaboration as possible among those analysts.
To foster that collaboration, BrightPoint Security has added to its Sentinel Security Command Platform a BrightPoint Security Exchange capability for tracking IT security threats identified using machine learning algorithms.
BrightPoint Security CTO Rich Reybok says IT security analysts need a mechanism through which they can share information about, for example, attack patterns being employed by digital criminals. To facilitate those conversations, analysts using the Sentinel Security Command Platform can now avail themselves of threaded conversations with peers in their Trusted Circles while maintaining the same access control to align with attribution and publishing policies. They can also attach documents, share tools and search conversations for threat data elements. IT analysts can generate queries and orchestrate security information event management (SIEM) and endpoint technologies directly from within those threads.
This latest release adds support for security management tools from Tanium and Intel to the existing support for tools from Carbon Black, Hive, Elastic, HP ArcSight, IBM QRadar, RSA Security Analytics and Splunk.
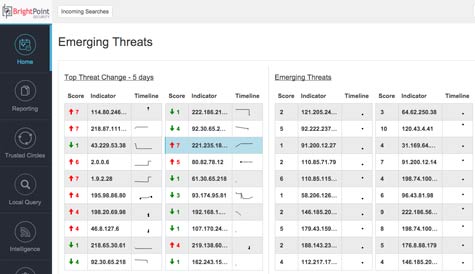
Other new features include an enhanced dashboard for tracking threat trends and associated metrics. For example, IT security analysts can view both their current threat risk rating as well as ratings of others in their Trusted Circle communities. Threat data sources and feeds can also be measured for their effectiveness in identifying critical risks within the context of how much of the IT security budget they consume.
In the wake of the recent Cybersecurity National Action Plan issued by President Barack Obama, Reybok says IT security analysts now have a freer hand when it comes to collaborating. Before, many IT security analysts could not collaborate because there are rules in place that prevent people working in organizations that compete with one another from sharing information. Obviously, IT security is one of those places where a well-intentioned mandate is getting in the way of a greater good. In fact, it apparently takes a presidential order to create a cybersecurity center of excellence and a national testing lab through which companies can legally share attack information.
In the meantime, IT organizations should take a cue from merchants of the old days when confronted with similar threats. Forced to confront piracy on the high seas, merchants shared information and armed convoys of ships that traveled together for their mutual defense. Some ideas, no matter how old they might be, still apply.