
Six Mobile Management Implications of iOS7
Just about everyone agrees that mobile computing is becoming critically important across the enterprise. Where disagreement manifests itself is in how to manage it. Many folks insist the only way to manage a fast moving mobile environment is with a dedicated mobile device management (MDM) platform, while others contend mobile will ultimately amount to little more than a natural extension of existing IT service management (ITSM) frameworks.
With the acquisition of Fiberlink Communications, a provider of MDM software, IBM is betting on both. According to Phil Buckellew, vice president of enterprise mobile for IBM, Fiberlink will become part of a larger IBM mobile computing management strategy that includes the Trusteer software that IBM acquired for managing and securing mobile applications aimed at consumers and Worklight, an IBM mobile application development platform that includes capabilities for managing and securing mobile applications.
Buckellew says Fiberlink adds an MDM component to IBM’s strategy for managing mobile computing devices used within a corporate context, regardless of whether they are owned by the company or employee. Over time, Buckellew says those offerings will then be integrated with IBM’s existing portfolio of ITSM to create a unified device management platform that can be delivered either on premise or the cloud. In addition, Buckellew says the portfolio of MDM technologies that IBM offers will be integrated with QRadar, the security intelligence software that IBM gained when it acquired Q1 Labs in 2011.
In the meantime, Buckellew says IBM plans to unify the software development kits (SDKs) surrounding all the technologies to create a seamless experience from the time the application is developed, through when it is deployed, and then ultimately when it is secured and managed.
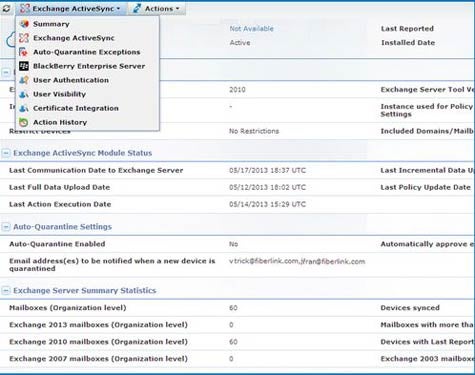
Buckellew says IBM acquired Fiberlink because its software is considerably simpler to use and easier to set up. In addition, as a platform built from the ground up for MDM, Buckellew says Fiberlink took care to create a layered approach to managing mobile security that ultimately provides a more secure mobile computing environment. In time, Buckellew contends that mobile computing will be even more secure than traditional PCs because mobile devices make it easier to incorporate location-based services into the security management process.
With the evolution of the mobile enterprise it’s pretty clear that IT organizations need to change the way they have traditionally thought about IT management. Rather than focusing on devices, the issue now is how to manage users that routinely employ multiple types of devices to access multiple corporate applications. In that context, IT organizations not only need new service desk tools, they also will have to change almost every aspect of the workflow processes that have now been in place for more than two decades. When all is finally done, that may wind up being the hardest challenge for mobile computing in the enterprise.
