Organizations put a lot of effort into keeping data within their networks safe, using any of a number of endpoint protection systems and monitoring tools. Unfortunately, once outside the safety of the corporate firewall, corporate data is exposed to threats both seen and unseen. Today’s workforce is on the move, working from remote locations almost as much as from a stationary office. To accommodate this fluidity of workplace, mobile devices are now carrying more sensitive corporate data than ever before, making them a prime access point for potential data breaches.
While organizations have been grappling with the complexities of BYOD, there’s definitely plenty of room for improvement. The facts highlighted in this slideshow, provided by Druva, aren’t for the faint of heart, so leave a light on while you learn about the dangers faced by data in the wild. And turning a blind eye won’t make them go away.
Data in the Wild
Click through for some very scary stats on the dangers faced by data in the wild, provided by Druva.
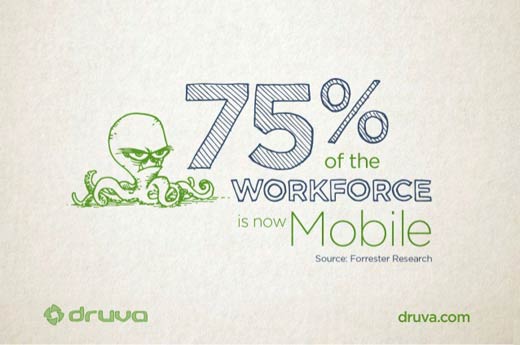
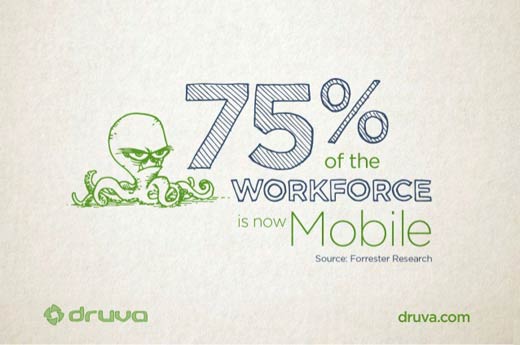
Seventy-five percent of today’s workforce is now mobile, and they take data everywhere. According to Cisco IBSG Horizons, the average employee has more than three connected devices at any time, and 70 percent of them access corporate data on personal devices.
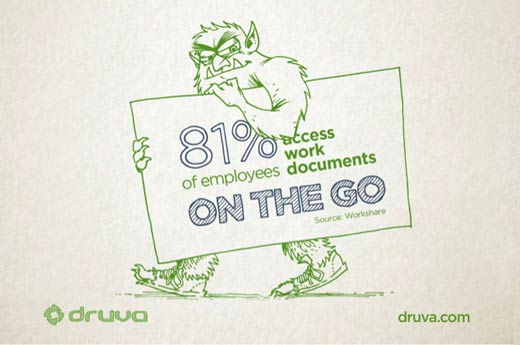
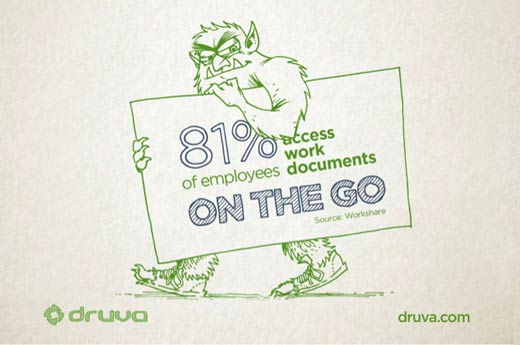
Employees don’t just work in the office anymore. They often work from multiple locations in any given week, and nearly half of employees telecommute at least one day a week. And, while not in the office, they need access to corporate data, just like everyone else. Workshare has determined that 81 percent of employees access work documents on the go.
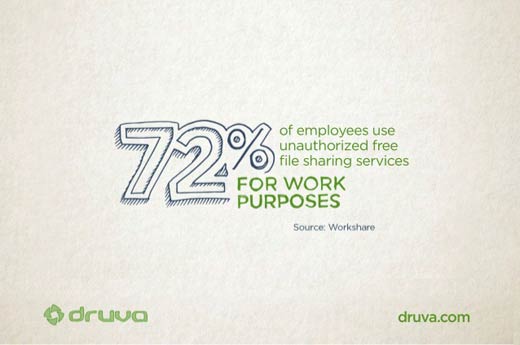
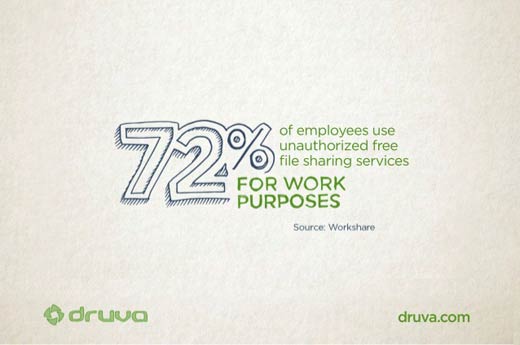
When you consider how a data breach occurs, your first thought is likely going to be hackers. And they do account for a large percentage of breaches, but nearly 36 percent of all data breaches are caused by inadvertent insider misuse. Even though 77 percent of companies have policies prohibiting the use of free online file-sharing services, 72 percent of employees report using them anyway. The Ponemon Institute also found that only 32 percent of organizations took steps to ensure employees didn’t wrongfully transfer or misuse information.
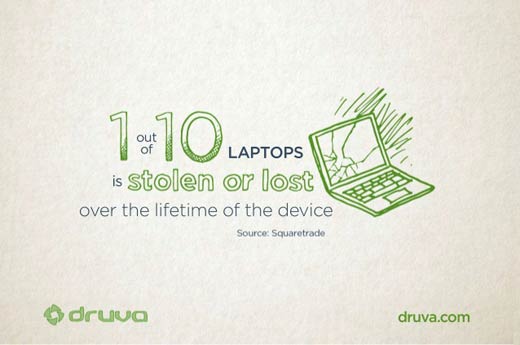
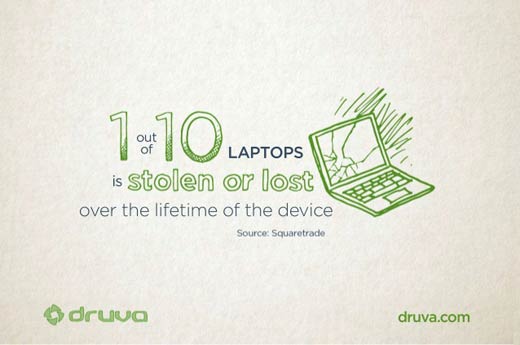
The use of mobile devices, such as laptops, also puts corporate data at risk. Squaretrade found that one laptop is stolen every 53 seconds, and over its lifetime, one in 10 laptops is either stolen or lost. This is particularly dangerous since 70 percent of corporate laptops are not encrypted and 90 percent do not have the ability to remotely wipe the laptops. Given the amount data stored on laptops, more than half of the stolen laptops result in a data breach.
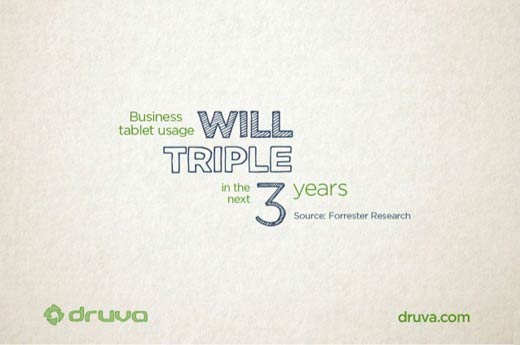
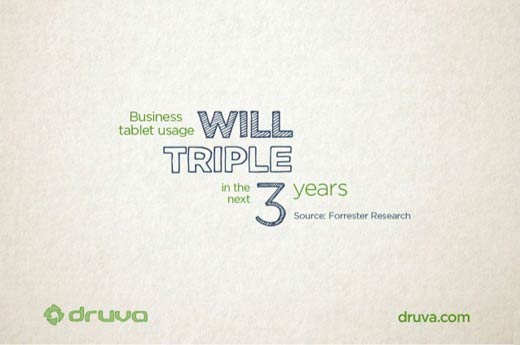
If you think stolen or lost laptops are scary, phones and tablets are even worse. According to Cisco, 90 percent of U.S. workers use their own smartphone for work, and 43 percent of executives use tablets. Business use of tablets is expected to triple over the next three years, exponentially increasing the endpoints that could be breached.
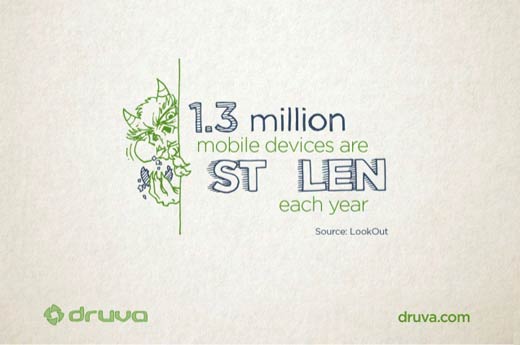
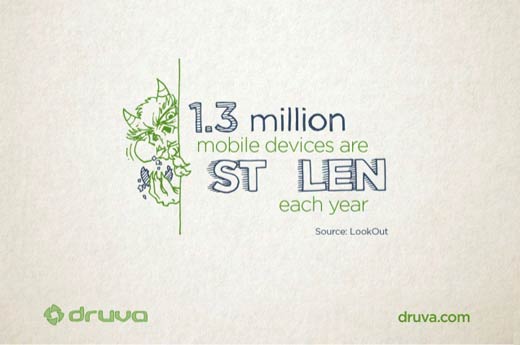
Every year, 1.3 million devices are stolen. Every 3.5 seconds, someone in America loses a cell phone, and phone theft has risen over 40 percent since 2007. These numbers are particularly terrifying given that 65 percent of companies are not able to remotely wipe devices, and 43 percent of mobile devices are not even password protected. The use of encryption could be a last-stand measure against a breach, but 76 percent of companies do not encrypt mobile devices carrying their data.
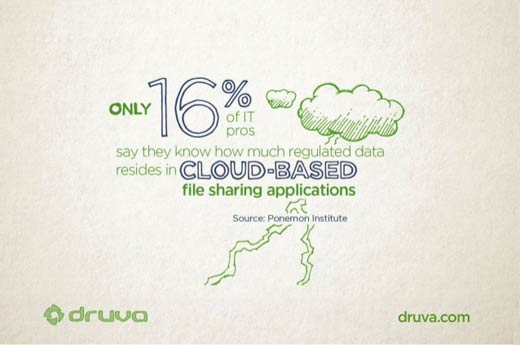
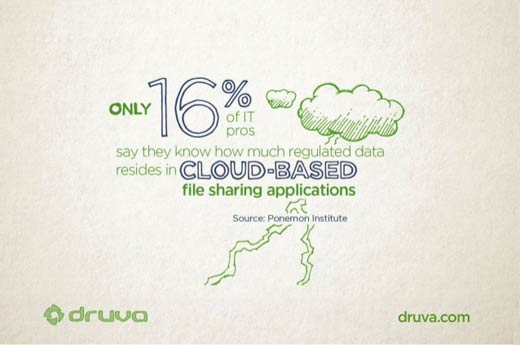
Governing data is a trick in our mobile world. First, you have to know how much regulated data is even on your endpoint devices. Unfortunately, 81 percent are not aware of how much regulated data they have on mobile devices. Even fewer (16 percent) are aware of how much regulated data resides in cloud-based file-sharing apps.
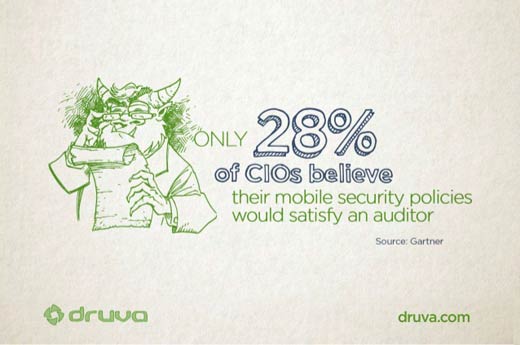
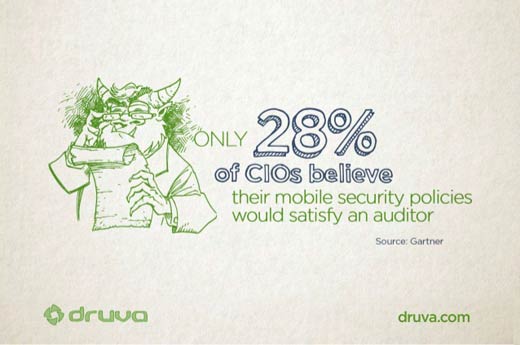
When it comes to an audit, most organizations would be up a creek without a paddle. Seventy-two percent of IT pros say it’s difficult to detect whether employees are using insecure endpoint devices, and only 28 percent of CIOs believe their mobile security policies would satisfy an auditor. Forty percent of IT pros can’t determine their organization’s compliance with employee access and use of regulated data on endpoint devices. Only 51 percent of companies are confident they can preserve data on mobile devices for litigation, regulator or investigative requirements.