The real challenge with security is that as the IT environment becomes more complex, it becomes more difficult to secure it. Most organizations recognize that they need to take a more proactive approach to managing security, but the complexity of the IT environments makes developing a more sophisticated security strategy cost-prohibitive. In an ideal world, IT organizations would have access to a set of security intelligence services that automate the IT organizational response to both existing and emerging threats.
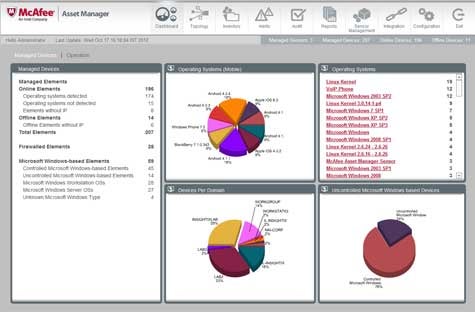
At the McAfee Focus 12 Security Conference today, McAfee took a significant step towards making that vision a reality with an update to McAfee Vulnerability Manager that adds McAfee Asset Manager software that automatically discovers and inspects devices as they connect to the network. That data is then fed back to McAfee ePolicy Orchestrator software to allow IT to apply security policies to any unmanaged device.
According to Roger Wood, McAfee director of product management, this combination of offerings is a significant step towards creating a unified set of security intelligence services that makes it possible for IT organizations to take information about threats discovered by McAfee’s Global Threat Intelligence service to dynamically apply security policies to any device on the network regardless of who owns it. As part of that effort, the Intel security subsidiary today is also updating its endpoint security offerings to include support for root-kit protection technologies that McAfee jointly developed with Intel along with support for the latest iOS operating system from Apple and more sophisticated application white listing capabilities.
In effect, Wood says McAfee is moving towards a model where security protection is provided continuously versus being something that is only invoked in response to an event. The challenge has been bringing together all the technologies for the framework needed to create a security management fabric that is capable of supporting the protection of IT at all layers of the environment.
While there will never be such a thing as perfect security, the cost of applying a more effective set of integrated security services that are highly automated is starting to drop to a point that is more affordable for most organizations. As the trend continues to develop, the overall IT security situation should start to substantially improve in the years ahead, even as cyber criminals and other digital miscreants continue to launch more sophisticated and targeted attacks. That, of course, may smack some as being nothing less than a security arms race. But it’s also a race that very few organizations can really afford to lose.