Five Predictions for the Connected Enterprise in 2014 As popular as Macintoshes and iPads from Apple are with the average end user, from an IT perspective, they represent a lot of additional complexity. Generally speaking, the tools that IT organizations have at their disposal are not applicable to Apple devices, resulting in a lot of […]

Five Predictions for the Connected Enterprise in 2014

As popular as Macintoshes and iPads from Apple are with the average end user, from an IT perspective, they represent a lot of additional complexity. Generally speaking, the tools that IT organizations have at their disposal are not applicable to Apple devices, resulting in a lot of manual support activities around operating systems that many IT folks are not as intimately familiar with as they are with Windows.
With the latest release of its Casper Suite of management tools for Apple devices, JAMF Software is looking to make it easier to manage Macs in the enterprise by providing tools that simplify device setup, automatically apply fixes, and prevent end users from removing profiles defined by internal IT.
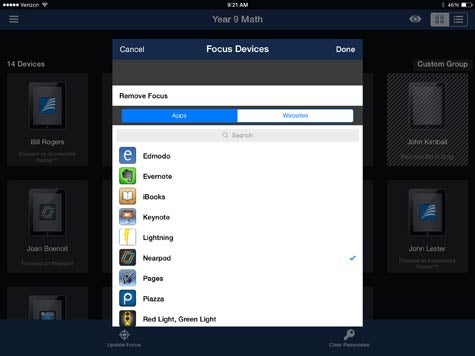
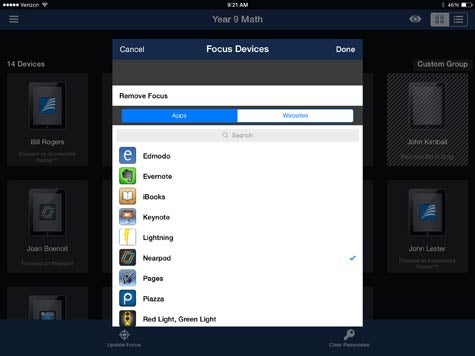
In addition, the Casper Suite 9.3 includes tools that allow IT organizations to re-assign apps to different users, invite users to install applications, control what software runs on an iPad, and even lock an iPad to a specific Web page.
JAMF Software CTO Jason Wudi says these capabilities leverage the Volume Purchase Program and Device Enrollment Program that Apple has created to make its devices easier to manage. JAMF Software, says Wudi, is now extending those Apple capabilities into the enterprise via a suite of management tools that is specifically designed to manage Apple systems and devices.
Wudi says that the one thing that distinguishes Apple from an IT management perspective is that Apple assumes that every device is going to have a mix of personal and corporate data on it. As such, Apple has made it easier to partition the management of data on its systems in a way that allows IT to more easily add and remove corporate data without affecting personal data.
As IT management continues to evolve, it’s becoming increasingly important for IT organizations to be able to manage systems at a data level that recognizes that, regardless of the official rules, end users have a mix of corporate and personal data on any given system. Being able to distinguish what type of data applies to what scenario is going to be the difference between IT being able to successfully navigate the Bring Your Own Device (BYOD) era and being seen as the enforcer of yet another set of corporate policies that end users are going to end run via whatever shadow IT service happens to be most readily available.
MV
Michael Vizard is a seasoned IT journalist, with nearly 30 years of experience writing and editing about enterprise IT issues. He is a contributor to publications including Programmableweb, IT Business Edge, CIOinsight and UBM Tech. He formerly was editorial director for Ziff-Davis Enterprise, where he launched the company’s custom content division, and has also served as editor in chief for CRN and InfoWorld. He also has held editorial positions at PC Week, Computerworld and Digital Review.