Federal, state and local governments are migrating to cloud services to take advantage of greater collaboration, agility and innovation at lower cost. However, despite clear benefits, 89 percent of IT professionals in government feel apprehension about migrating to the cloud.1 That being said, many public sector employees are less apprehensive and are adopting cloud services on their own, creating shadow IT. Under FITARA, U.S. federal CIOs have new obligations to not only oversee sanctioned cloud services procured by the agency, but also shadow IT, which has brought to light a great deal of uncertainty about how employees are using cloud services in government agencies.
To better understand these trends, Skyhigh Networks has published a “Cloud Adoption & Risk in Government Report.” Findings were based on anonymized usage data for over 200,000 users in the public sector in the United States and Canada, rather than relying on surveys, which ask people to self-report their behavior.
1 Meritalk “The Fabric of Your Data: How to Manage Data in a Multi-Cloud, Multi-Vendor Environment”

Public Sector Cloud Usage
Click through for findings from a study looking at public sector usage of cloud services including “shadow IT,” conducted by Skyhigh Networks.
Cloud Adoption and Risk
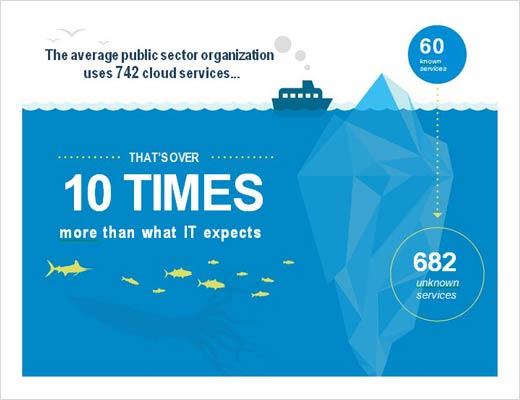
The average U.S. federal agency takes 18 months to define and procure a new software solution, and 54 percent of employees say their agency is not able to acquire IT in a timely manner. This drives employees to find their own solution, producing “shadow IT.” The average public sector organization now uses 742 cloud services, which is 10 to 20 times more than what is known by the IT department.
Cloud Usage
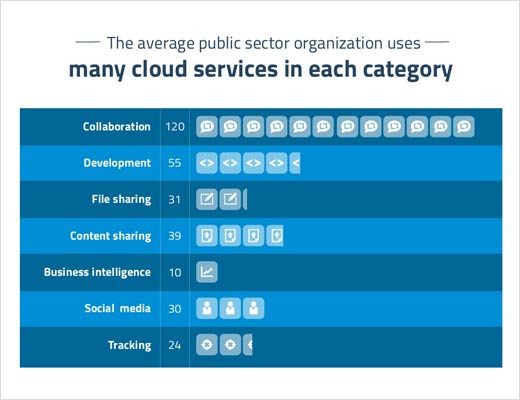
By far, the top category of cloud usage in the public sector is collaboration. The average organization uses 120 distinct collaboration services (e.g., Microsoft Office 365, Gmail, etc.), followed by 55 software development services (e.g., SourceForge, GitHub, etc), 31 file sharing services (e.g., Dropbox, Google Drive, etc.), and 39 content sharing services (e.g., YouTube, LiveLeak, etc.).

Calculated Risk
Public sector organizations have unique security concerns. U.S. federal agencies estimate that 32 percent of their data cannot be moved to the cloud due to security and data sovereignty issues.3 Of course, the security controls offered by cloud providers vary widely. Analyzing more than 10,000 cloud services across over 50 attributes of enterprise-readiness developed with the Cloud Security Alliance, Skyhigh found that just 9.3 percent achieved the highest CloudTrust Rating of Enterprise-Ready. Only 10 percent of cloud services encrypt data stored at rest, 15 percent support multi-factor authentication, and 6 percent have ISO 27001 certification.
Compromised Identities
Over the last two years, data breaches have become a fact of life. On an almost daily basis, news hits about another big breach that has potentially compromised data ranging from passwords to Social Security numbers to medical information.
According to a study by Joseph Bonneau at the University of Cambridge, 31 percent of passwords are reused in multiple places. The implication here is that, for 31 percent of compromised identities, an attacker could not only gain access to all the data in that cloud service, but potentially all the data in the other cloud services in use by that person as well.
Considering the average public sector employee uses more than 16 cloud services, and 37 percent of users upload sensitive data to cloud file-sharing services, the impact of one compromised account can be immense.
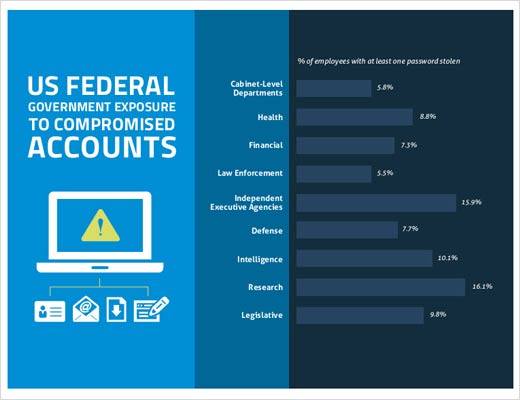
Skyhigh found that 96.2 percent of public sector organizations have users with compromised identities. At the average organization, 6.4 percent of users have at least one account that has been compromised. At the time of their analysis, they found that some accounts had been updated with new passwords, while many others remained active with compromised identities.
Insider Threats
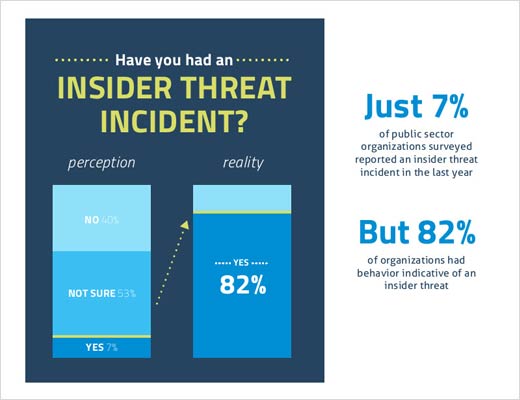
With the Cloud Security Alliance, Skyhigh surveyed IT and IT security professionals in the public sector and found that only 7 percent indicated that their organization had experienced an insider threat in the last 12 months. However, looking at actual anomaly detection data, they found 82 percent of companies had behavior indicative of an insider threat in the last quarter alone. While not all insider threats involve leaking data to the media, the risk of malicious and careless insiders is much higher than previously believed.

Top 20 Enterprise Cloud Services
The top 20 list is dominated by cloud heavyweights: Microsoft (Office, Yammer, SharePoint Online, OneDrive), SAP (ERP, SuccessFactors, Concur), Cisco (WebEx), Oracle (Taleo) and Salesforce. It also includes several independent companies that have gone public in the last several years, including ServiceNow, Box and Jive. The list is heavily weighted toward collaboration (six services), file sharing (four services) and finance services (four services). Of the top 20 enterprise cloud services, 17 are delivered by companies headquartered in the United States.

Top 20 Consumer Apps in the Enterprise
Today, many consumer applications are so useful, employees use them in their everyday work. This can cause headaches for IT if government data is stored in unsanctioned cloud services known as “shadow IT.” Attackers can also use these services as vehicles to exfiltrate data. For example, Skyhigh discovered attacks that targeted sensitive company IP, and then leveraged Twitter to exfiltrate the stolen data 140 characters at a time. Their security intelligence team also identified a novel attack that steals sensitive data by encoding the data into video files before uploading them to YouTube, where attackers can then download the information and decode it.

File Sharing, Collaboration and Social Media
File Sharing
The average public sector organization uses 31 file sharing services and the average employee uses 1.3 services. Well-known services Google Drive and Dropbox top the list this quarter. U.S. government organizations may be troubled to find Russian-hosted Yandex.disk on the list and may want to investigate what data employees upload to this service.
Collaboration
The use of collaboration services in government is pervasive. The average organization uses 120 services and the average employee regularly uses 2.8 distinct collaboration services. Microsoft takes three spots on the list with Office 365, Yammer and Hotmail. Conferencing service Cisco WebEx continues to lead GoToMeeting.
Social Media
The average public sector organization uses 30 social media services and the average employee regularly uses 2.6 services. Twitter, Facebook and LinkedIn continue to top the list. A relatively new service, Tumblr, is a micro-blogging platform that allows governments to connect with constituents in a new way.
