Five Things to Do Now for Greater Security and Compliance Manually combing through logs looking for anomalies that might represent a security threat is not only tedious, it also introduces a level of security fatigue that makes it more likely for a security threat to go unnoticed. To help organizations reduce that risk, Splunk developed […]

Five Things to Do Now for Greater Security and Compliance

Manually combing through logs looking for anomalies that might represent a security threat is not only tedious, it also introduces a level of security fatigue that makes it more likely for a security threat to go unnoticed.
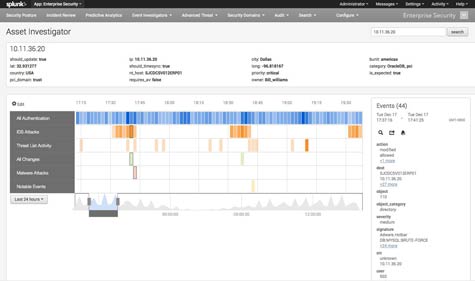
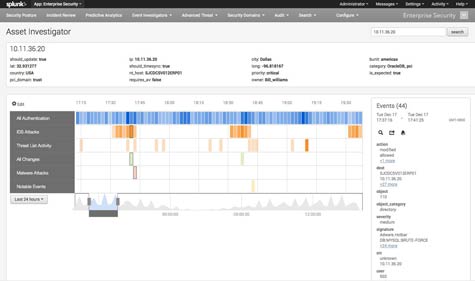
To help organizations reduce that risk, Splunk developed its Splunk App for Enterprise Security, which applies analytics to logs in a way that makes it a lot easier to identify the patterns that represent potential security threats. Released this week, version 3.0 of the app adds support for a new threat intelligence framework, additional data types and data models, and a pivot interface.
Mark Seward, senior director of security and compliance for Splunk, notes that the logs that security professionals are trying to monitor are growing in size, and they are also made up of a lot more varied types of data. Asking security professionals to manually comb through all that data is generally inefficient and it turns IT security into a chore that most IT professionals will be more apt to neglect.
Tools that visualize those threats, notes Seward, even the odds for security professionals in a way that makes the cat and mouse game of security a whole lot more satisfying because it takes less time and it increases the odds of successfully blocking attacks.
Another benefit of the Splunk App for Enterprise Security, adds Seward, is that most organizations subscribe to multiple security threat news feeds, most of which deliver multiple warnings about the same security threat. In an age when security is a manual effort, those warnings prompt IT organizations to take preventative actions by identifying the same threat multiple times over. Because Splunk App for Enterprise Security allows IT to more easily identify security patterns, Seward says the staff can reduce their dependency on multiple security threat feeds that spew out redundant threat information.
Invariably, IT organizations wind up chasing down vulnerabilities based on variants of the same basic threat over and over again. A more efficient way of identifying and keeping track of both the number of threats and the potential damage they actually represent is clearly necessary. Like most wars, data security involves extended periods of boredom punctuated by moments of sheer terror. Helping the troops stay alert and at the ready is the primary responsibility of the officers that manage those troops.
MV
Michael Vizard is a seasoned IT journalist, with nearly 30 years of experience writing and editing about enterprise IT issues. He is a contributor to publications including Programmableweb, IT Business Edge, CIOinsight and UBM Tech. He formerly was editorial director for Ziff-Davis Enterprise, where he launched the company’s custom content division, and has also served as editor in chief for CRN and InfoWorld. He also has held editorial positions at PC Week, Computerworld and Digital Review.