Turning Zero-Day into D-Day for Cybersecurity Threats Not everyone appreciates the fact that not all intelligence is equally relevant or, for that matter, actionable. Much these days has been made about security intelligence, but all too often what is provided is data relating to a potential security breach that lacks any context. To solve that […]

Turning Zero-Day into D-Day for Cybersecurity Threats

Not everyone appreciates the fact that not all intelligence is equally relevant or, for that matter, actionable. Much these days has been made about security intelligence, but all too often what is provided is data relating to a potential security breach that lacks any context.
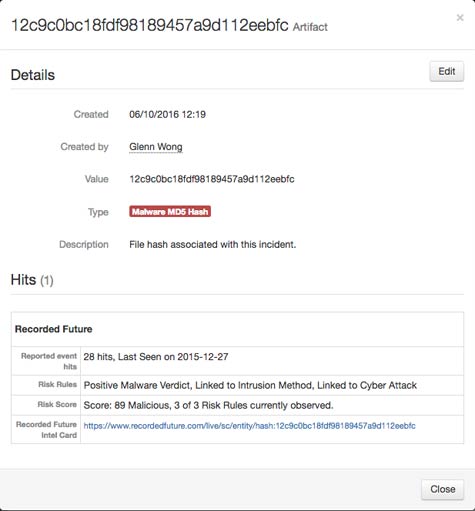
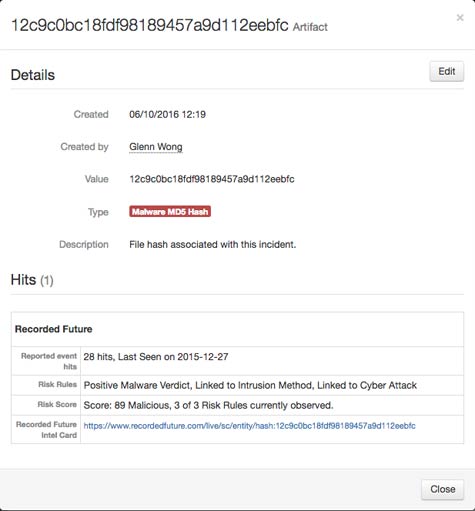
To solve that issue, Recorded Future created a security intelligence service that makes use of text mining and analytics to better correlate security intelligence without relying solely on the experience of a security analyst to figure out what might be occurring before anything bad happens. At the Gartner Security & Risk Management Summit 2016 conference this week, Recorded Future advanced that capability by announcing that it has extended that service via connectors to share data with security products and services from Palo Alto Networks; Resilient, an IBM company; and FireEye iSIGHT Intelligence.
Matt Kodama, vice president of product for Recorded Future, says other connectors and integrations will soon follow suit as Recorded Future moves to provide what for all intents and purposes used to require a level one security analyst to provide. Automating that analysis doesn’t eliminate the need for security analysts. But it does make security analysts that are already in short supply more effective. The truth is that even when IT organizations can find a good security analyst, they generally can’t afford to keep them because competition for their services is acute.
For that reason, many IT organizations are increasingly looking to machine learning and other forms of artificial intelligence (AI) to level the IT security playing field. It’s too early to say what effect these technologies will have on making enterprise IT organizations more secure. But a limited number of IT security professionals will be able to cover more ground in a finite amount of time.
Of course, it’s only a matter of time before cybercriminals start leveraging machine learning algorithms and maybe even one day AI to identify vulnerabilities faster. Like it or not, IT security is pretty much an arms race, where the difference between winning and losing will, like in any war, come down to who has the best intelligence.
Save
Save
MV
Michael Vizard is a seasoned IT journalist, with nearly 30 years of experience writing and editing about enterprise IT issues. He is a contributor to publications including Programmableweb, IT Business Edge, CIOinsight and UBM Tech. He formerly was editorial director for Ziff-Davis Enterprise, where he launched the company’s custom content division, and has also served as editor in chief for CRN and InfoWorld. He also has held editorial positions at PC Week, Computerworld and Digital Review.