Oracle is pushing to eliminate the silos that have long existed between IT security and compliance via an update to the Oracle Identity Security Operations Center (SOC) cloud service. Rohit Gupta, group vice president for cloud security at Oracle, says the latest version of Oracle Identity SOC makes it possible to determine how changes to […]
Oracle is pushing to eliminate the silos that have long existed between IT security and compliance via an update to the Oracle Identity Security Operations Center (SOC) cloud service.
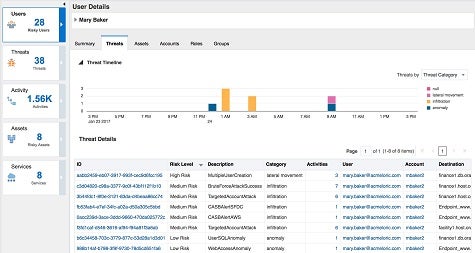
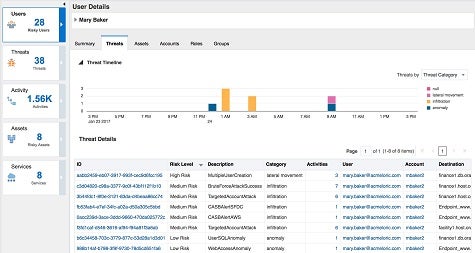
Rohit Gupta, group vice president for cloud security at Oracle, says the latest version of Oracle Identity SOC makes it possible to determine how changes to providing access to applications might impact the overall IT security posture of an organization. For example, when a user is given access to a new application, Oracle SOC applies advanced analytics and machine learning algorithms to the feeds being generated via the Oracle Cloud Access Security Broker service to determine the potential impact that change might have on the security of other applications, says Gupta. In addition, Gupta says IT organizations can use that capability to identify what credentials are no longer being used. Those capabilities are enabled by tightening integration between Oracle Identity SOC and the Oracle Cloud Compliance service that is part of Oracle Management Cloud.
Those same analytics, adds Gupta, can be employed to determine what ports are open or whether encryption has been inadvertently turned off. IT organizations can then determine if they want those ports to be automatically turned off or encryption enabled by default, says Gupta.
Oracle is also integrating Oracle Identity SOC with Oracle Marketing Cloud and Oracle Data Cloud, which makes it possible for IT organizations to extend those identity management and compliance capabilities to external-facing applications.
Finally, Oracle has unfurled Identity SOC Security Network in Oracle Cloud Marketplace to provide connectors to third-party security technologies spanning enterprise mobility management, firewalls, endpoint security and threat intelligence services.
Gupta says IT organizations want to be able to more flexibly and consistently apply security policies by relying on cloud services based on application programming interfaces (APIs). In many instances, Gupta says, that need is being driven by the unification of IT security and application development, otherwise known as DevSecOps.
“We’re trying to take security to another level,” says Gupta.
It is too early to say whether such a shift will result in more secure IT environments. But given the current state of IT security in the enterprise, there’s little doubt that a more programmatic approach that brings IT security and compliance processes closer together would represent a significant step in the right direction for most IT organizations.
MV
Michael Vizard is a seasoned IT journalist, with nearly 30 years of experience writing and editing about enterprise IT issues. He is a contributor to publications including Programmableweb, IT Business Edge, CIOinsight and UBM Tech. He formerly was editorial director for Ziff-Davis Enterprise, where he launched the company’s custom content division, and has also served as editor in chief for CRN and InfoWorld. He also has held editorial positions at PC Week, Computerworld and Digital Review.