Cyber Crime Report Finds Old Breaches Led to New Breaches For some time now, Niara has been making the case for using behavioral analytics to help IT organizations identify normal user activity versus activity that would suggest that a particular user account has been compromised by cybercriminals. This week, Niara added support for machine learning […]

Cyber Crime Report Finds Old Breaches Led to New Breaches

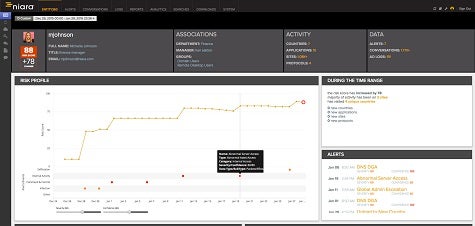
For some time now, Niara has been making the case for using behavioral analytics to help IT organizations identify normal user activity versus activity that would suggest that a particular user account has been compromised by cybercriminals. This week, Niara added support for machine learning algorithms optimized to help IT organizations identify systems that have been compromised by ransomware and other types of “spear phishing” malware.
Niara CEO Sriram Ramachandran says the goal is to enable IT organizations to identify as soon as possible abnormal behavior involving, for example, the encrypting of data that an end user would not normally need to access. With the information the IT organization can then implement the appropriate “kill chain” strategy to isolate that end user account to limit the amount of potential damage that ransomware might be able to inflict, says Ramachandran.
While most IT organizations would prefer to do everything they can to prevent malware from infecting their systems in the first place, the fact remains that defenses against ransomware attacks are fairly limited. In general, these attacks rely on social engineering tactics that fool end users into downloading advanced malware directly onto to their machines. Beyond more aggressively backing up data, no amount of investment in traditional firewalls is going to make a difference when an end user bypasses those defenses by directly loading malware on to their own machine.
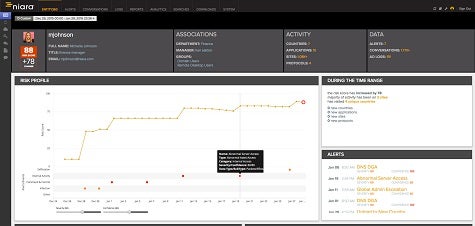
Ransomware attacks are exploiting the soft underbelly of IT by exploiting end users. The challenge many IT organizations face when supporting hundreds, sometimes even thousands, of end users is that it’s hard for an individual IT administrator to identify normal behavior for any specific end user, much less when it’s actually occurring.
Nevertheless, IT organizations are being judged less by the amount of malware they stop at the perimeter. Instead, the focus now is on how quickly they can identify cybersecurity threats, which systems are compromised by that threat, and how quickly the issue can be remediated.
Faced with that challenge on a daily basis, it’s clear that IT organizations are going to need to rely more on analytics to identify what is normal end user behavior. End users may not always appreciate the inquiries from IT every time they want to do something that may be out of the norm. But with so much now riding on digital business strategies, it’s hard to see what else IT organizations can do to protect businesses that increasingly depend on immediate access to data to both engage customers and conduct transactions.
Save
Save
MV
Michael Vizard is a seasoned IT journalist, with nearly 30 years of experience writing and editing about enterprise IT issues. He is a contributor to publications including Programmableweb, IT Business Edge, CIOinsight and UBM Tech. He formerly was editorial director for Ziff-Davis Enterprise, where he launched the company’s custom content division, and has also served as editor in chief for CRN and InfoWorld. He also has held editorial positions at PC Week, Computerworld and Digital Review.