Most IT organizations today struggle with trying to keep up with who is connecting which device to an extended corporate network that is accessing some set of unknown applications. To provide some visibility into those events, ForeScout Technologies developed an agentless approach to provide IT organizations with visibility into and control over both distributed endpoints […]
Most IT organizations today struggle with trying to keep up with who is connecting which device to an extended corporate network that is accessing some set of unknown applications. To provide some visibility into those events, ForeScout Technologies developed an agentless approach to provide IT organizations with visibility into and control over both distributed endpoints and public clouds such as Amazon Web Services (AWS).
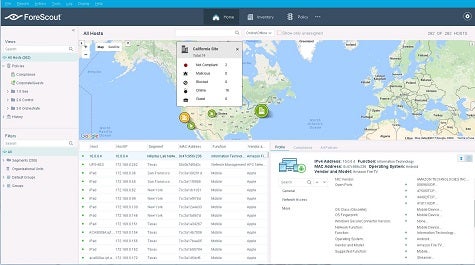
ForeScout today announced it is now extending the reach of the ForeScout CounterACT platform into software-defined data centers (SDDCs) based on the VMware platform, including VMware NSX network virtualization software. In addition, ForeScout announced that the latest version of ForeScout CounterACT can now scale to manage over one million devices, many of which ForeScout has already pre-classified to accelerate deployments.
Rob Greer, chief marketing officer for ForeScout, says given the highly distributed nature of enterprise computing, most organizations today find it difficult to maintain compliance, let alone secure their environments.
“They have a big visibility problem,” says Greer.
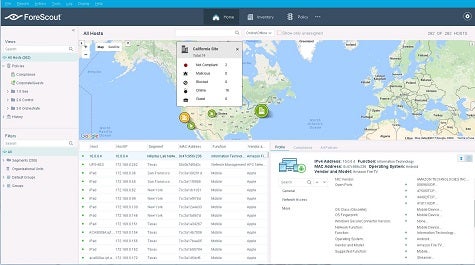
Because the ForeScout approach doesn’t rely on agents to be deployed on each individual endpoint, Greer says ForeScout makes it possible for IT organizations to both easily discover new devices and applications being connected to the corporate network and apply the appropriate policies without first having to deploy agent software on them. Greer say IT organizations can even customize the rules as they see fit. There’s also a crowdsourcing option through which customers can optionally share new IoT device fingerprints via the CounterACT device profile library.
Finally, ForeScout has implemented a new user interface to make it simpler to manage the overall environment.
These days, IT security and compliance is all too often a thankless job. In fact, it’s not really all that fair to hold IT professionals accountable for events they have no way of knowing occurred in the first place. The only way to resolve that constraint is to employ some form of an agentless overlay that makes up for that lack of intelligence.
MV
Michael Vizard is a seasoned IT journalist, with nearly 30 years of experience writing and editing about enterprise IT issues. He is a contributor to publications including Programmableweb, IT Business Edge, CIOinsight and UBM Tech. He formerly was editorial director for Ziff-Davis Enterprise, where he launched the company’s custom content division, and has also served as editor in chief for CRN and InfoWorld. He also has held editorial positions at PC Week, Computerworld and Digital Review.