5 DDoS Myths Debunked In the wake of a series of high-profile distributed denial of service (DDoS) attacks that compromised various types of consumer devices and crippled popular websites, the awareness of the security threat these devices potentially represent is now a lot higher. But determining which Internet of Things (IoT) devices on a corporate […]

5 DDoS Myths Debunked

In the wake of a series of high-profile distributed denial of service (DDoS) attacks that compromised various types of consumer devices and crippled popular websites, the awareness of the security threat these devices potentially represent is now a lot higher. But determining which Internet of Things (IoT) devices on a corporate network might be vulnerable to these attacks is another matter.
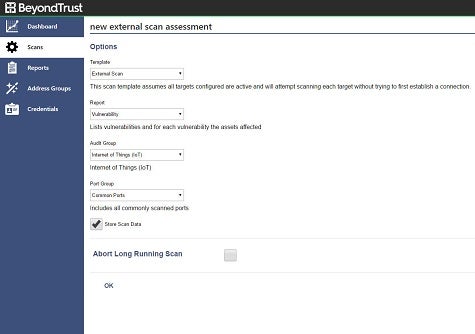
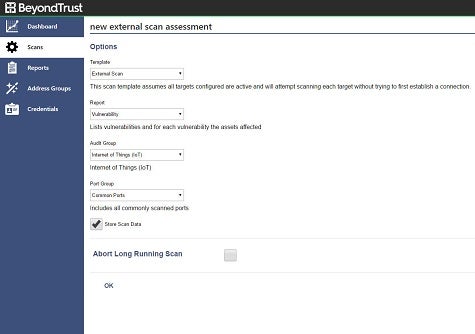
To make that easier for IT organizations to accomplish, BeyondTrust is making available a free version of its vulnerability scanner that is optimized for IoT environments. Morey Haber, vice president of technology for BeyondTrust, says the Retina IoT (RIoT) Scanner is based on the same technology that BeyondTrust developed to identify vulnerabilities across the rest of the enterprise.
RIoT Scanner, says Haber, is a cloud service that IT organizations can invoke to identify the make and model of specific IoT devices and any associated vulnerabilities, including checking default and hard-coded credentials used in conjunction with Telnet, SSH or basic HTTP authentication. RIoT Scanner also generates reports and remediation guidance.
Haber says organizations need to be extra vigilant about allowing employees to connect consumer-class devices to the corporate network. Historically, many employees have routinely connected everything from webcams and wireless routers to Amazon Echo devices. These devices are creating a new class of infrastructure that needs to be secured, says Haber.
“It’s really an extension of the BYOD (bring your own device) phenomenon,” says Haber.
The issue is that hackers are now actively scanning the internet looking for devices that can be incorporated into a botnet they have created to launch a DDoS attack.
BeyondTrust is not making any bones about the fact that it hopes organizations that make use of RIoT will discover the merits of the commercial vulnerability scanning service it provides for the rest of the enterprise. In the meantime, IT organizations would be well advised to remember that it’s usually some seemingly innocuous device connected to the network that winds up being the source of the most harm.
Save
MV
Michael Vizard is a seasoned IT journalist, with nearly 30 years of experience writing and editing about enterprise IT issues. He is a contributor to publications including Programmableweb, IT Business Edge, CIOinsight and UBM Tech. He formerly was editorial director for Ziff-Davis Enterprise, where he launched the company’s custom content division, and has also served as editor in chief for CRN and InfoWorld. He also has held editorial positions at PC Week, Computerworld and Digital Review.