Navigating Your Way Through an IT Road Map At the Black Hat USA 2016 conference today, Armor, a provider of a secure hosting facility, announced that it is extending the framework it uses to secure data inside its own data centers out to the rest of the enterprise. Jeff Schilling, chief security officer for Armor, […]

Navigating Your Way Through an IT Road Map

At the Black Hat USA 2016 conference today, Armor, a provider of a secure hosting facility, announced that it is extending the framework it uses to secure data inside its own data centers out to the rest of the enterprise.
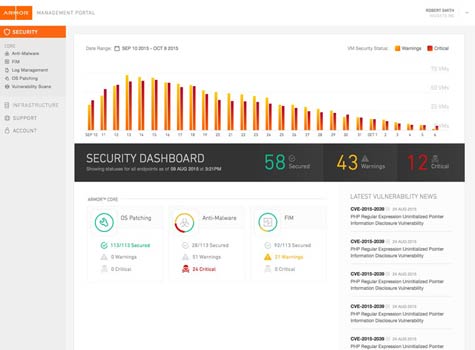
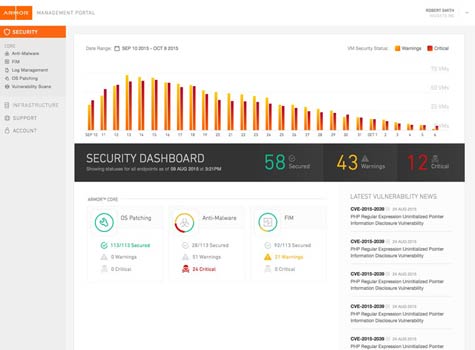
Jeff Schilling, chief security officer for Armor, says the company, formerly known as FireHost, has created Armor Anywhere agent software that IT organizations can now attach to any virtual machine regardless of where it resides. That agent software then enables Armor to remotely monitor that virtual machine to keep IT organizations informed about every change made to it.
In an IT world where organizations now routinely distribute virtual machines across both public cloud and third-party hosting services, Schilling says Armor Anywhere makes it possible for IT organizations to make sure those virtual machines have not been tampered with in any way. That’s crucial from both a security and compliance perspective, when IT organizations have to prove they are able to maintain control over highly distributed computing environments, adds Schilling.
Once it is installed, IT organizations can then make use of a security operations center (SOC) built by Armor to monitor those virtual machines or contract Armor to provide a set of managed security services that perform that function on their behalf. Those services span threat intelligence, patch monitoring, log and event management, malware protection, file integrity monitoring and external vulnerability scans.
Given the scope of the security threats most organizations face, Shilling says very few of them are going to be able to combat those threats on their own. By continuously looking for any indications of compromise, Armor not only helps ensure the integrity of those virtual machines, Schilling says it helps reduce the overall total cost of security by offloading that task from the IT department.
At a time when IT security expertise is in short supply, IT organizations need to pick their battles. IT security by definition requires mastering multiple layers of complex products and services. The odds that most internal IT organizations are always going to do that well without relying on external security expertise are indeed low.
Save
Save
MV
Michael Vizard is a seasoned IT journalist, with nearly 30 years of experience writing and editing about enterprise IT issues. He is a contributor to publications including Programmableweb, IT Business Edge, CIOinsight and UBM Tech. He formerly was editorial director for Ziff-Davis Enterprise, where he launched the company’s custom content division, and has also served as editor in chief for CRN and InfoWorld. He also has held editorial positions at PC Week, Computerworld and Digital Review.