In a survey of 72 healthcare organizations, conducted by the Ponemon Institute on behalf of ID Experts, a provider of data breach prevention software, it’s clear that the loss of mobile computing devices and breaches caused by third-party applications are contributing to the problem. It's also clear that most health care organizations do not have the processes or funding in place to deal effectively with these issues, and that there is a marked increase in the number of incidents related to identity theft.
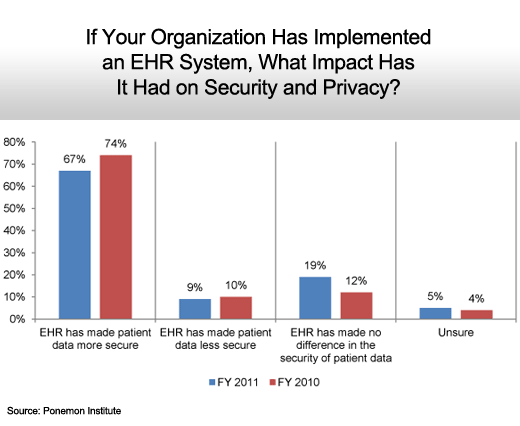
The overall conclusion of the study is that there has not been much progress made in health care security in the last year, with one notable exception: Organizations that have implemented electronic health records (EHR) are reporting that security has improved significantly as part of the process of digitizing medical records.
Click through for results from a health care security survey, conducted by the Ponemon Institute on behalf of ID Experts.
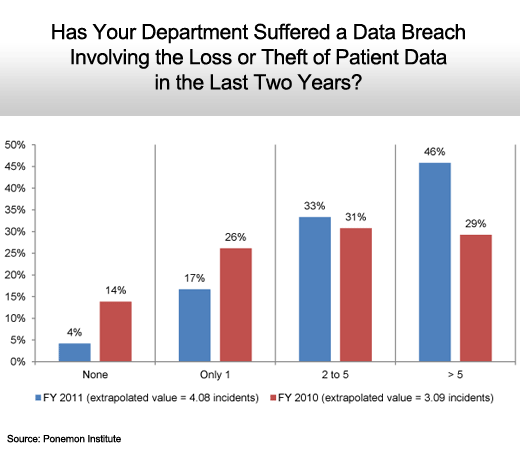
The number of security incidents is up significantly.
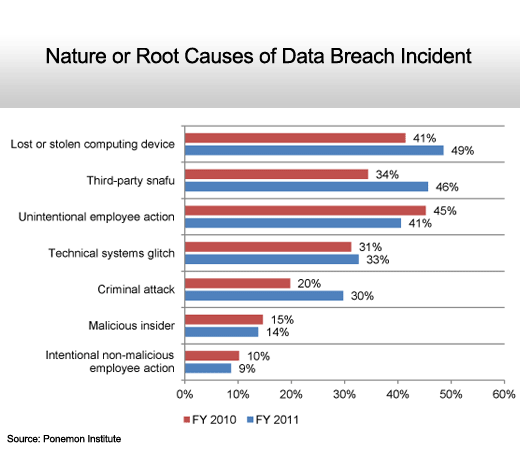
Lost devices are closely followed by third-party application software.
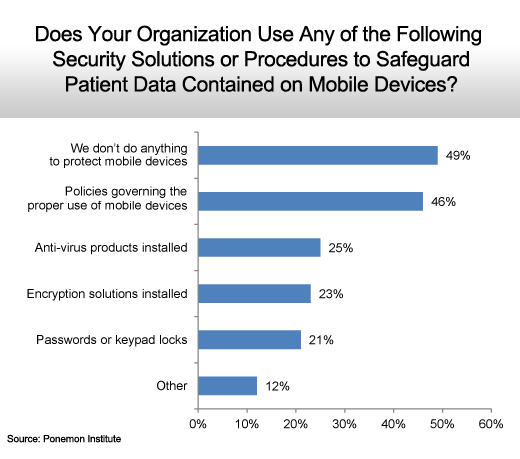
Many health care organizations don’t have sufficient mobile security technology in place.
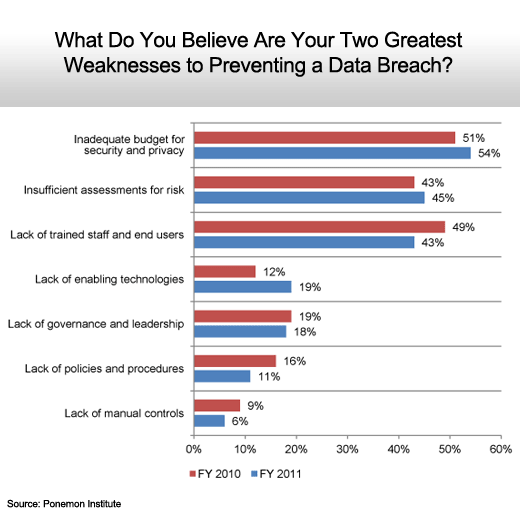
Budget, awareness and training top the list.
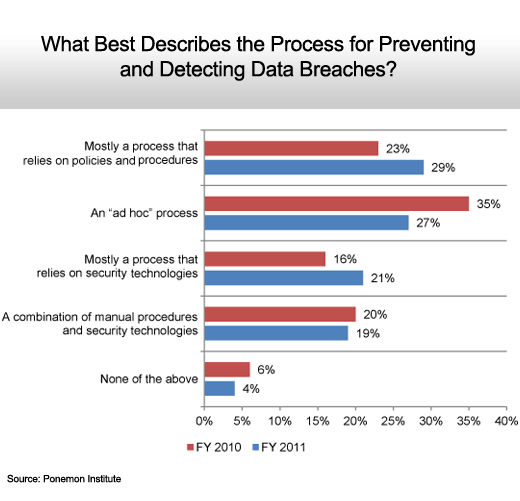
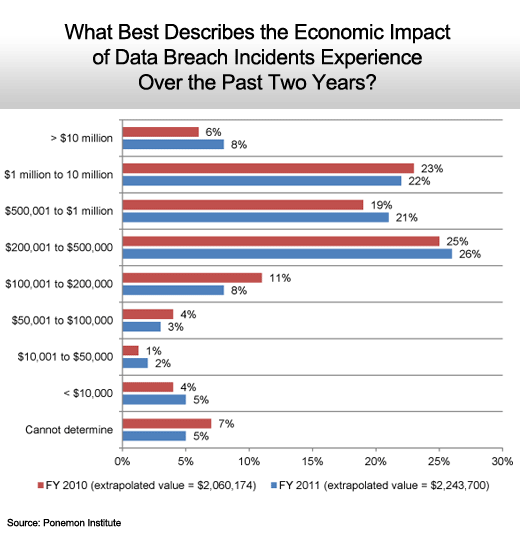
Not much change year over year.
Slow but steady progress.
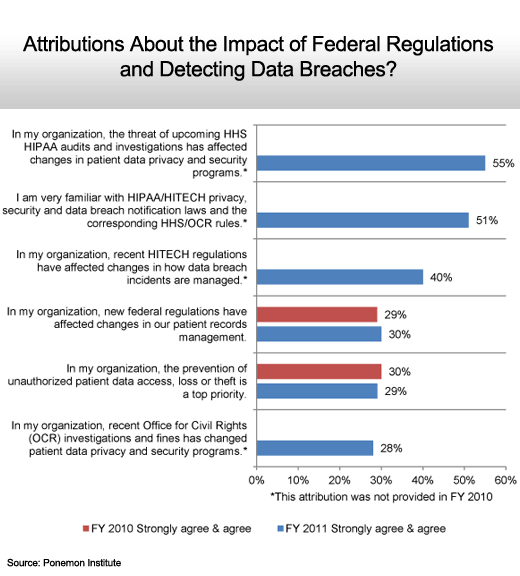
Tighter rules and regulations are having an effect.
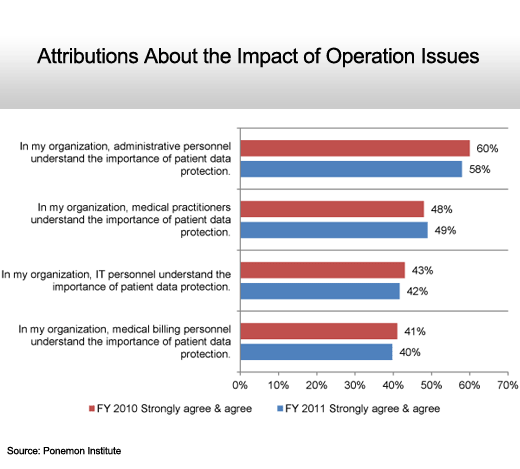
Not much progress.
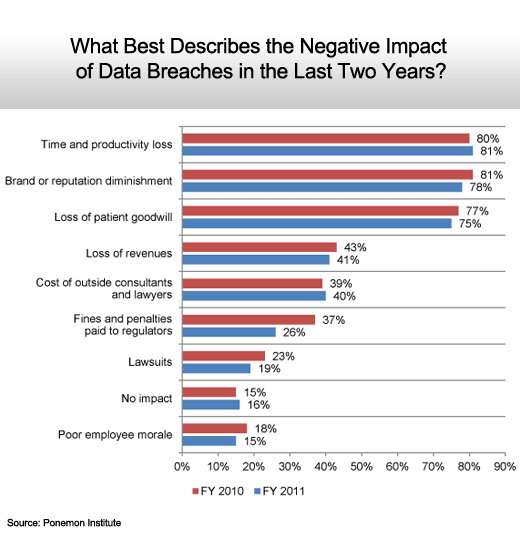
The only attribute that dropped significantly was fines and penalties.
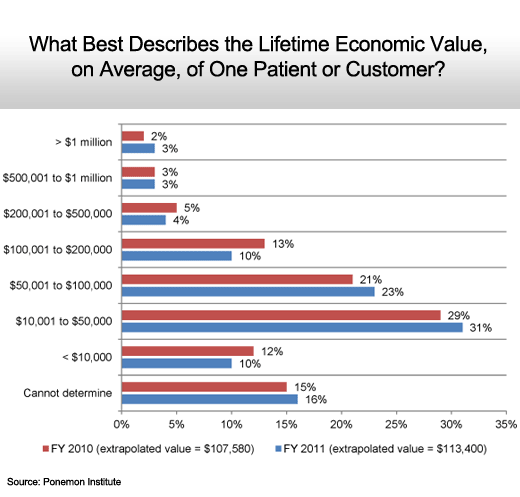
Patient values continue to creep upwards.
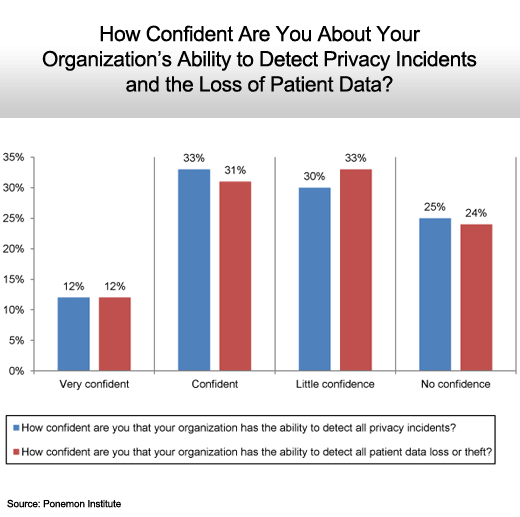
Roughly equal.
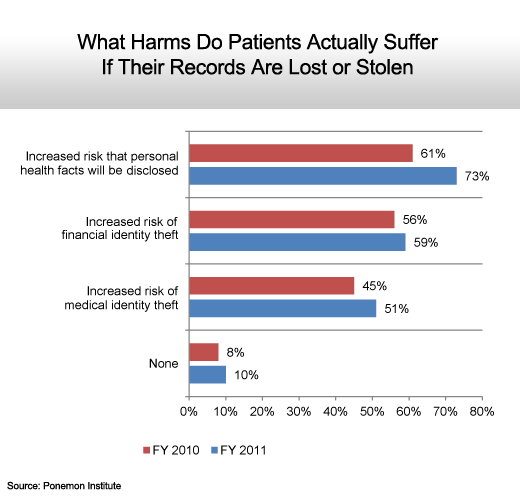
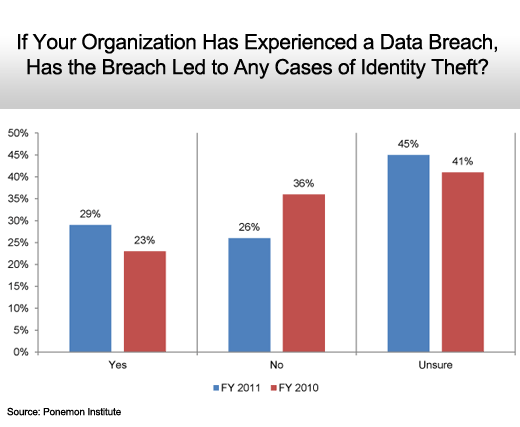
Identity theft is on the rise.
The threat becomes an increasing reality.
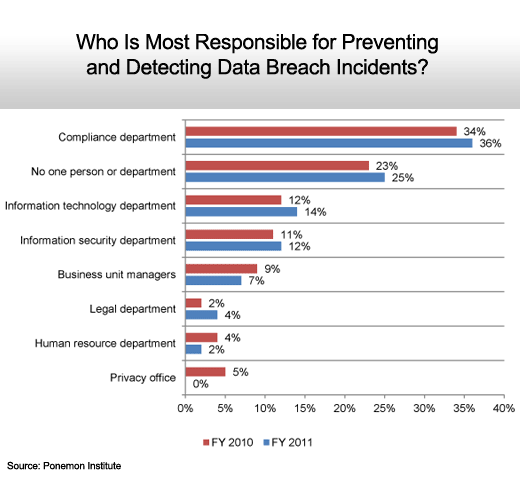
The compliance department when there actually is one.
EHR actually improves security.