I could use a hackneyed phrase and call the coming smartphone challenge the “Perfect Storm.” But I won’t. There are two reasons, the first because it’s a hackneyed phrase, and let’s face it, the Storm (a BlackBerry iPhone wanna-be) is far from perfect. But the fact is, the explosive growth of smartphones is going to give IT managers one of their biggest challenges since people started trying to bring their own personal computers into the office.
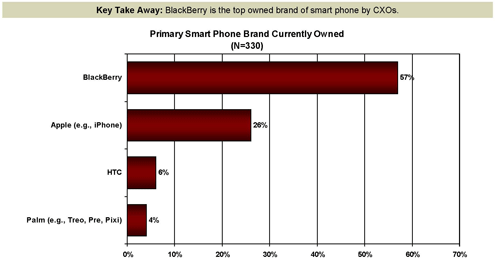
In some ways, however, the problem is bound to be worse now than the PC revolution ever was in terms of IT complexity. First of all, smartphones cost a lot less than computers did in those days, so there are a lot more of them, and second, there’s the sheer diversity. Where we may have had three or four basic platforms back in the early days of PCs, we have dozens of smartphone platforms with, according to research data from Frost & Sullivan, BlackBerries and the Apple iPhone being the most popular among senior executives.
But even among the majors, there’s a pretty long list. Every enterprise has to deal with Apple, RIM and Microsoft. Most also have to deal with Palm or Android, some with Nokia. The list could go on for a long time.
While there was a brief time when IT managers could dictate that their departments would only support a small subset of devices, say Microsoft and RIM, we’re already past that. Employees are already buying the latest, coolest devices. Most of those devices come with clients that will connect with the company Exchange server, and some with clients for other enterprise e-mail systems. In many cases, there’s not a lot that an IT manager can do to prevent such connections except perhaps restrict the entire company from using Web mail.
Fortunately, the problem isn’t hopeless, but without some quick forward-looking plans, it’s going to get out of hand pretty quickly. First, acknowledge that you’re stuck with smartphones owned by employees at all levels, and embrace that rather than fighting it. Second, develop some in-house expertise with specific types of smartphones so you can help employees get their connections to the corporate network done properly.
And finally, set guidelines for appropriate use, and for corporate support. Here are ideas that I’ve gathered from talking with a range of industry experts:
Openly allow smartphones with as few restrictions as possible. For example, the inability to connect to the corporate e-mail system seamlessly should be a non-starter. Then train employees on what to do if they lose their smartphone, stressing that there won’t be any penalties, but that you’ll need to cut off access to company e-mail as soon as possible.
Decide (maybe through employee input) which smartphones to actively support. Most likely that list will include phones from RIM, Apple and Microsoft and may include phones running Android. Palm sales are tanking so badly that those may not turn out to be an issue. Once you decide, offer at least limited support in connecting with the company network.
Allow people to pay for their phones and their service. Offer reimbursement to people who actually have a business need for them, and make sure that those phones you’re paying for meet your technical and security guidelines.
Get out of the business of buying phones completely except in very specific circumstances, such as those requiring unusually rugged construction, or those requiring access to classified information. This alone will save your company tons of money, and your employees will like the fact that they can pick the phone they want.
Make sure your infrastructure will support the growth in wireless devices such as smartphones. Almost all of them support Wi-Fi now, and some support voice over Wi-Fi. You need to plan your network around that.
Done properly, embracing and developing a role for smartphones in your enterprise can cut costs, improve employee morale and improve productivity. Done wrong (or not done at all) and you could easily find yourself in Smartphone Hell, with employees doing what they please, and the IT department having no say at all.
Click through these highlights from Frost & Sullivan’s comprehensive survey of CXO’s Mobile Computing Products & Services.
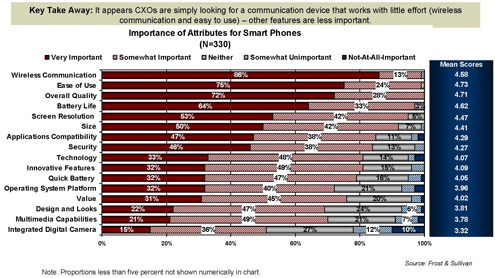
Wireless network access and ease-of-use top the agenda.
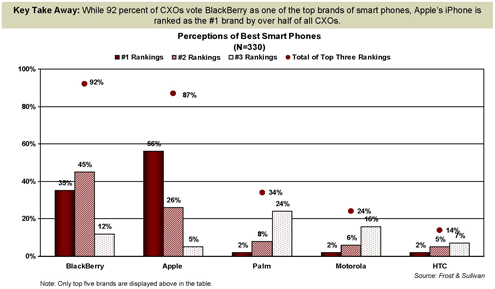
BlackBerries dominate, but the Apple iPhone is gaining.
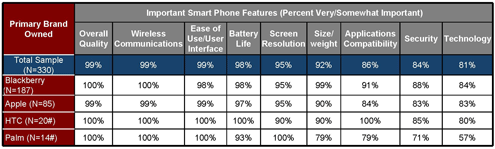
HTC scores well alongside BlackBerry and Apple iPhone.
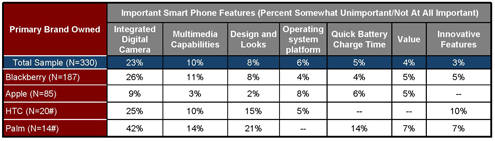
Camera capabilities are not a key consideration.
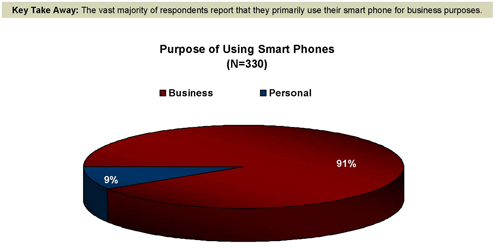
Vast majority of smartphone usage is for business.
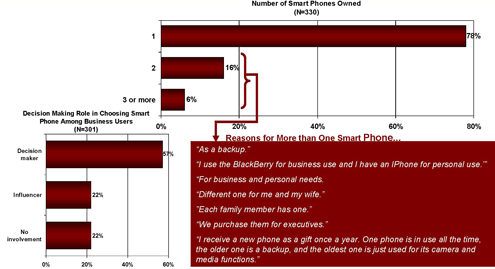
CXOs play a key role in deciding smartphone brand.
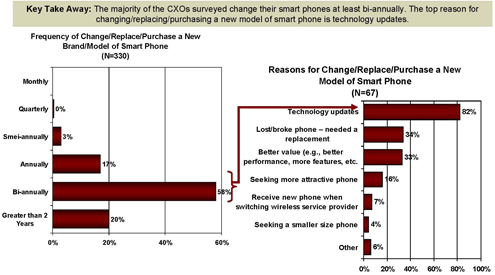
Shifts in purchases are tethered to length of service contracts.
Apple iPhone edges out the BlackBerry.
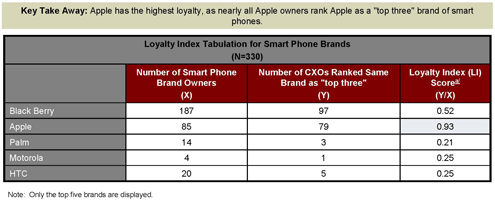
Apple also has the highest loyalty rating.
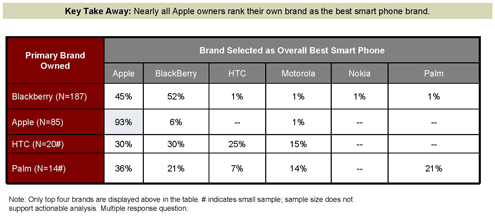
Apple is also considered the best brand in the category.
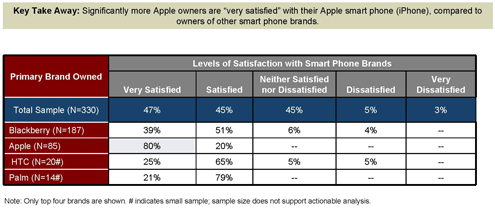
Apple iPhone also enjoys the highest satisfaction levels.
And more Apple iPhone users intend to buy more iPhones.