When times were good, malware attacks were pretty much the cost of doing business. They happened from time to time, but nobody ever really considered their real impact on the business.
Now that times are tough and the number of zero-day malware attacks have increased, the operational costs of security are becoming a much bigger factor.
That’s the primary finding of a survey of 564 IT security managers conducted by The Ponemon Institute on behalf of Lumension, which finds that security issues are becoming a bigger drain on limited IT resources.
The survey also finds that far too many IT organizations don’t have much in the way of control over security policies. Many report either not having any or simply lack the wherewithal to enforce them.
According to Ed Brice, senior vice president for worldwide marketing at Lumension, the study not only highlights the need for more effective policy enforcement, but it also shows that anti-malware software isn’t enough to make the overall IT environment secure. And without additional security measures, IT organizations are incurring significant additional operating expense cleaning up after malware infects their systems.
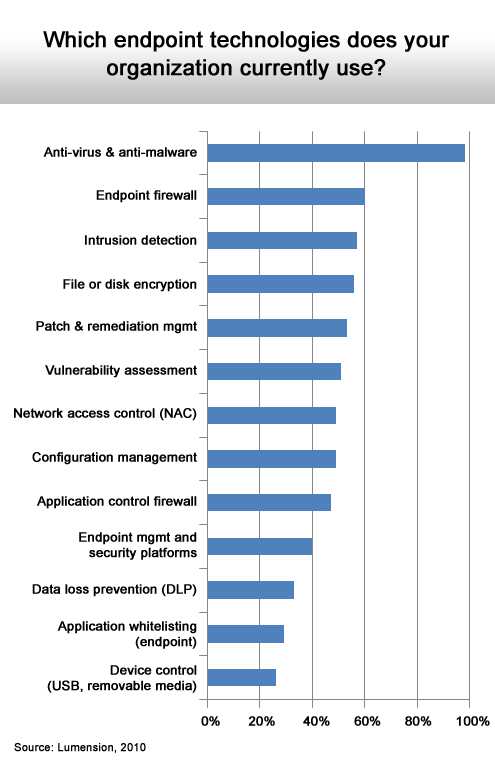
A comprehensive approach to security should not only include anti-malware software; IT organizations should be deploying application controls, policy-based management systems based on whitelisting techniques and data loss prevention (DLP) systems.
Unfortunately, the majority of the IT organizations surveyed by Lumension have yet to deploy any of these security technologies, even as their operational security costs continue to rise. Worse yet, with the rise of mobile computing in the enterprise, Brice contends that the security will become even more complicated to manage.
Of course, in these tough times, it’s sometimes hard to make a case for additional security investments. But when you start to factor in how much time and expense is being wasted in the aftermath of a malware infestation, suddenly the cost of security doesn’t look nearly as prohibitive.
Click through for results from a survey conducted by Lumensions on endpoint security risks.
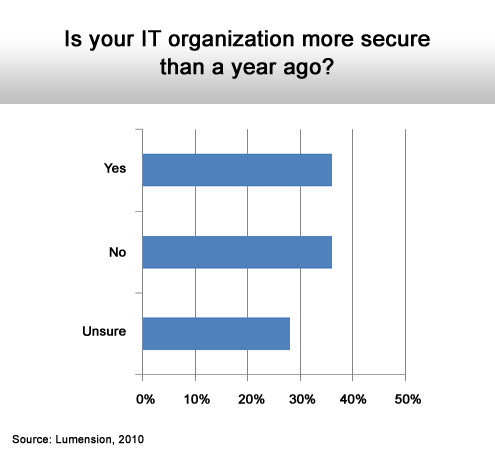
Confidence is low.
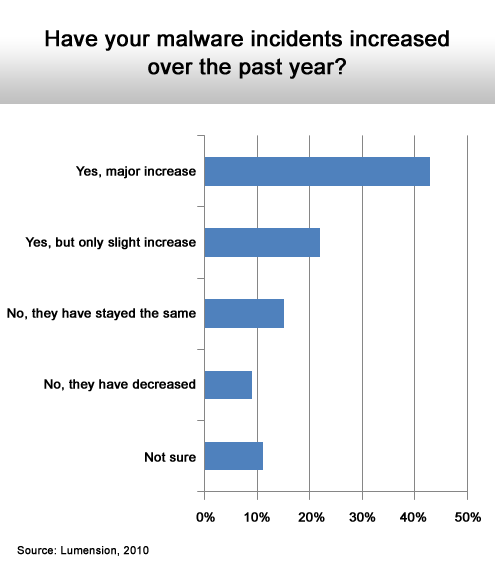
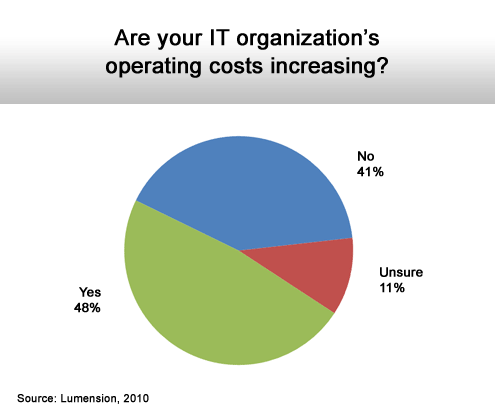
The trend is definitely heading in the wrong direction.
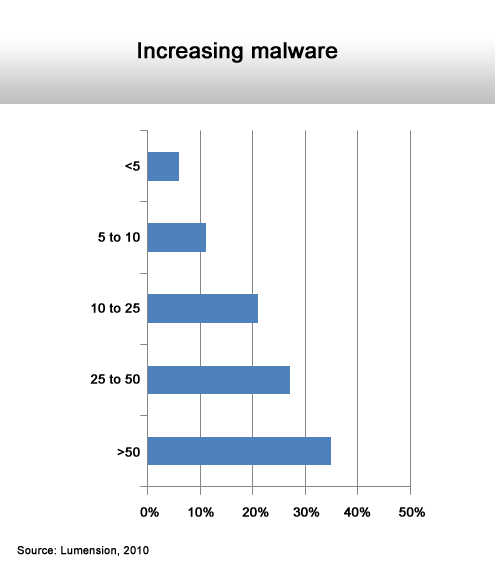
And many deal with 50 or more incidents.
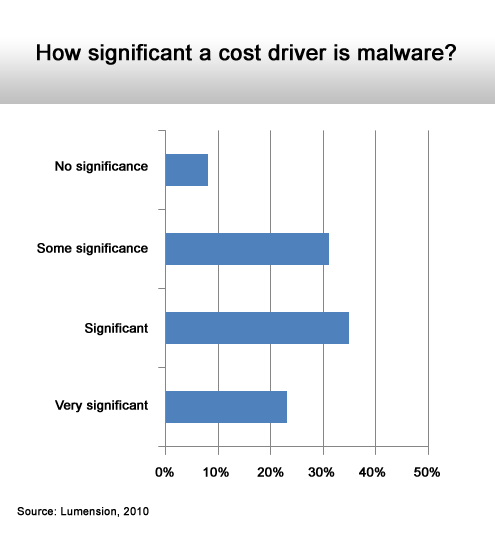
For many it is.
And it’s becoming a bigger issue with each additional attack.
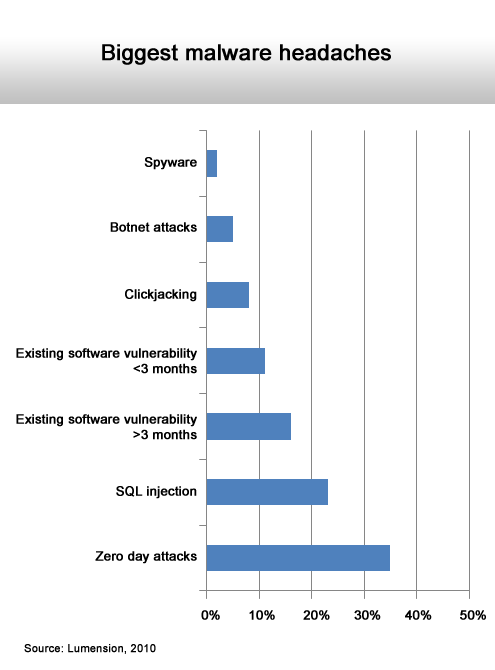
Zero day attacks leave no time to prepare a defense.
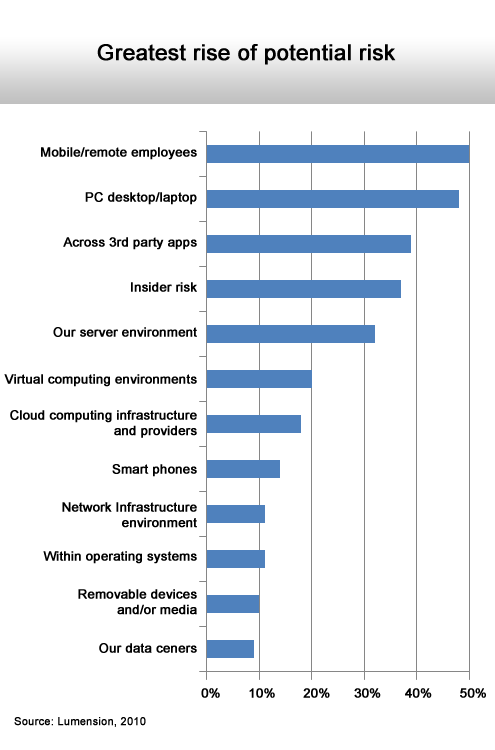
Mobile computing increases security risks.
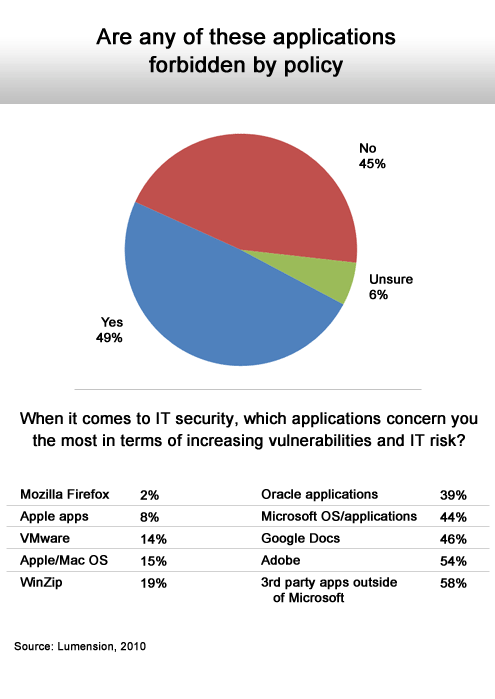
Only half have a policy drive approach to application deployment.
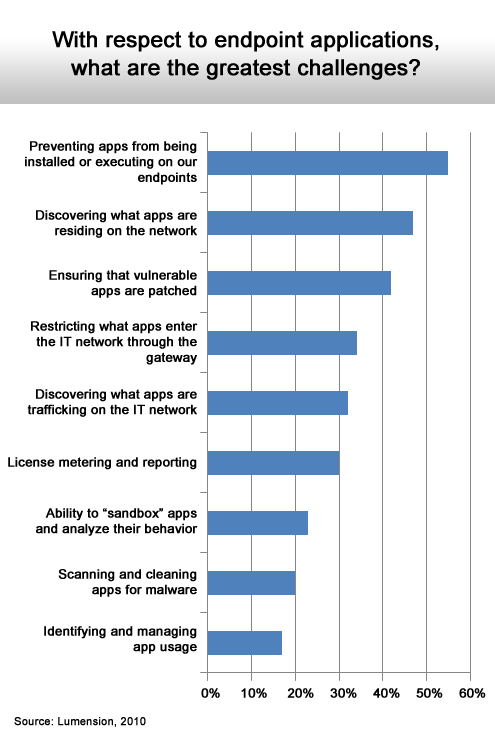
Seems like many IT organizations have no control over the endpoint.
Only about a third can discover all applications on the network.
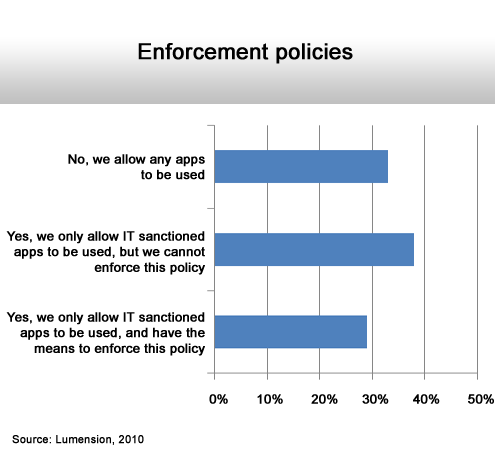
Most either don’t have one or can’t enforce the ones they have.
After anti-virus, use of security technologies falls off sharply.