We often think of information security as the realm of highly technical geeks, incomprehensible and happy to remain so. But the truth is that each one of us, as we learn to navigate an increasingly digital, mobile and social info-scape, is getting in touch with our ‘inner security geek.’ Information security has broken out of the confines of the technically elite and is becoming part of everyone’s job and day-to-day life. And that’s a good thing.
In this slideshow, Yo Delmar, vice president of GRC, MetricStream, has identified five reasons why information security has become everyone’s responsibility, not just the IT department.

Security Depends on Everyone
Click through for five reasons why information security has become everyone’s responsibility, not just the IT department, as identified by Yo Delmar, vice president of GRC, MetricStream.
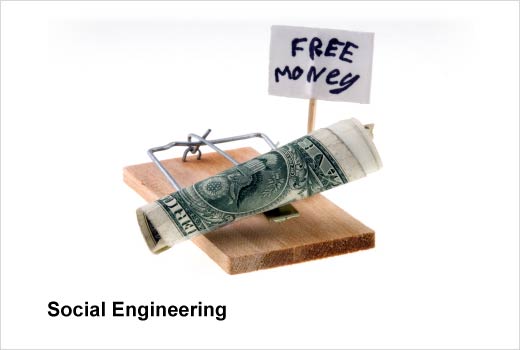
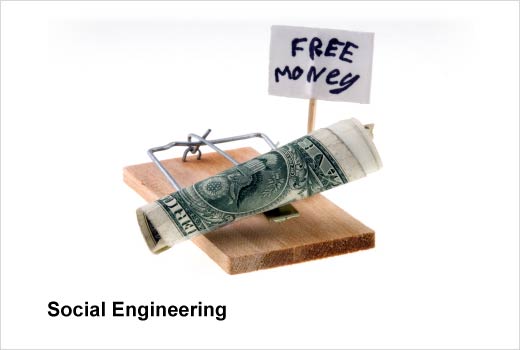
Social Engineering
Reason #1: Because the human being is becoming the primary attack vector.
Over half of all data breaches involve some kind of failure in security awareness. That means human beings are often the weakest link; we have become the primary attack vector. The majority of these attacks involve spear phishing, namely, online fraud attempts directed at specific individuals or companies.
Social engineering is often the first step in an attacker’s plan. You’ve heard the typical scenario. Somebody pretends to be someone you know, and then gets you to click on something that will deliver a damaging payload. Think about the critical steps along the Lockheed Martin Cyber kill chain – the attacker builds a portfolio of information on the target and exploits different vectors to gain access to sensitive and valuable assets. Attackers can gather loads of information from social networks and even sites like ancestry.com and alumni associations. The attacker might pose as a far-flung relative, a former classmate, or a colleague from the firm you worked at a decade ago before presenting the lure. And often enough, we click the link and are stung.
How do you nurture your inner security geek? Be wary about the information that can be gleaned from your publicly available information or through random contact with you. Take an extra moment to wonder why that person is approaching you now; ask yourself – does their story hold water? Be aware of social engineering, tighten up your defenses, and don’t take the bait.

Too Much Connectedness
Reason #2: Because we are far too interconnected.
As we blur the boundaries between work and personal systems, we connect ourselves through dozens of apps with single sign-on. For example, most apps now offer the convenience of logging in with Gmail or Facebook. When you do this, you are connecting your ‘locked’ information through what is essentially one key. It’s a double-edged sword that trades convenience for vulnerability to a chain of attacks with every new app you bring into the circle. You might benefit from the integrations between business systems. You may value fast access to information you have saved to your iPhone, Google Docs or Dropbox. The fatal flaw is that convenient interconnectedness brings the same ease of access to an attacker.
How do you nurture your inner security geek? The antidote is to reduce the connectedness. When you are offered the option to “log in with Facebook” to a particular app, simply don’t do that. Don’t increase your vulnerability to a chain of attacks through too many interconnections.

Rapid Tech Evolution
Reason #3 – Because workplace technology is evolving so rapidly, you need to help out.
New and burgeoning technology — from social to cloud, mobile, or the Internet of Things — brings escalating threats and vulnerabilities. A recent article in the Financial Times quoted cybersecurity chiefs who estimated that 90 percent of the vulnerabilities are known, and have known patches. But they just haven’t been remediated yet.
Your workplace IT and security teams suffer from limited budgets and limited staff. They struggle to prioritize investments in defenses for critical assets. Don’t make their job harder.
As we become more digitally connected in the workplace, contractors, suppliers and customers have access to all sorts of things that they didn’t have access to even five years ago. The pervasiveness of technology puts power at your fingertips, making it more important for you to become more conscious of what’s going on around you. The perpetrator of a security breach may be an insider. For example, Edward Snowden was a third-party consultant in the NSA. People around him knew he had elevated access, and some knew that he was doing some odd things. You might experience anomalies in your workplace, such as someone asking for access to your computer: “Can you lend me your password? I just have to check one little thing.” Ask yourself: Why is that person asking you to go against a norm or a policy or a process to satisfy their request? And don’t be afraid to say no.
How do you nurture your inner security geek? Whenever you see an anomaly in your digital work world – from a customer, supplier or fellow employee – report it. Do your bit to help out.

Threat Intelligence
Reason #4: Because crowdsourcing is wildly powerful.
Security teams use sophisticated technology to detect anomalies, but those monitoring systems catch only about 50 percent of fraudulent transactions. How are we going to collectively close the gap? Simply stated, we have to develop an information intelligence capability. Security awareness, leading to threat intelligence, has to be built into our behavior as we traverse the virtual landscape. We can move more quickly up the threat intelligence curve by being aware of, and acting on, things we observe.
People who are targeted in certain transactions often have the sense that something is a little off. We should not hesitate to dig deeper. For example, when you get an odd voice message, note the caller’s number, and what they said, and then Google it. Very often it comes up as a scam.
Some people think they don’t know enough about technology to make a difference, but the truth is that law enforcement agencies depend on ordinary people to help them solve cases. For example, at the Internet Crime Complaint Center (IC3), analysts use reported information as input to correlation systems to identify links and commonalities between various complaints and incidents, which are then combined and referred for law enforcement.
With cybersecurity breaches increasing every year, you might feel we will never be able to adequately protect our information. Instead of being overwhelmed, remember that the power of crowdsourcing is tremendous. When we put our ideas together and pool our observations, as James Surowiecki writes, there is the “wisdom of crowds.”
How do you nurture your inner security geek? If you see something, say something! The crowd is where the intelligence community gets a lot of their information against constant and pervasive threats. As individuals working together, we can boost both our personal and collective threat intelligence capability dramatically.

Privacy
Reason #5: Because privacy is being redefined by all of us.
It used to be that privacy of information was all about protecting regulated data. But now, your information is everywhere. It’s spread out, it’s ubiquitous, and we have lost control over it. For every online transaction – email, tweet or message – its digital shadow grows as copies are stored, backed up and archived on systems at your bank, service provider or intermediaries along the way. You couldn’t get your information back even if you tried. Once you’ve keyed or texted it, it’s out there.
The old notion of privacy is dead. The good news: Together, we as citizens have the power to redefine what the new model of privacy needs to be.
Privacy is not just about protecting every little piece of data. Privacy now refers to a trust relationship that we are party to and responsible to co-create. Consider the trust agreement with people who house your data. How are they going to use that data? How will your information fit in a bigger mosaic, or be used to interpolate something else about you that you don’t want others to know? For us to engage effectively in the dialogue, we have to become competent on these baseline issues. We must reflect on what and where the boundaries need to be placed. These are good discussions to become a part of as Big Data rapidly evolves our virtual info-scapes.
How do you nurture your inner security geek? Be an advocate of yourself and your information, and understand the trust relationship you are entering into when you accept policies around privacy. Join the dialogue as we redefine privacy and make your views known. We are all part of it. Consider this your ‘Inner Security Geek Call to Action’!