Top Trends Driving the Data Center in 2015 One of the primary concerns that IT organizations have with deploying containers is security. While containers are an emerging virtualization technology and have become popular with developers, IT operations teams are wary of deploying them in production applications because there is no mechanism for applying security controls […]

Top Trends Driving the Data Center in 2015

One of the primary concerns that IT organizations have with deploying containers is security. While containers are an emerging virtualization technology and have become popular with developers, IT operations teams are wary of deploying them in production applications because there is no mechanism for applying security controls to containers running on physical servers.
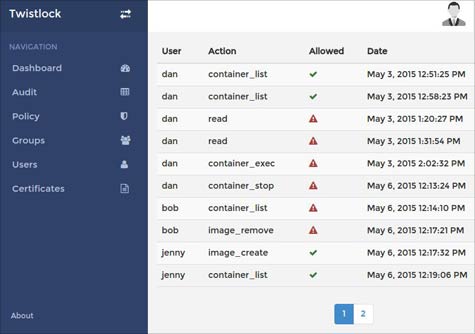
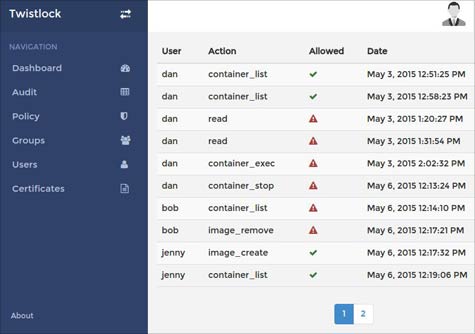
To address that issue, Twistlock today launched a namesake container security suite. These tools provide IT organizations with a console through which they can monitor both static container images and runtime container applications. They can also harden container hosts and images by applying security controls such as authentication and authorization.
Twistlock CEO, Ben Bernstein, says that IT organizations today are deploying containers such as Docker on top of virtual machines in order to apply security controls to those containers. But that approach requires making use of an additional layer of virtualization software. Longer term, Bernstein says Twistlock is betting that IT organizations will want to deploy containers in place of virtual machines to drive server utilization rates higher. In general, where 10 to 20 virtual machines can be deployed on a single physical server, it’s possible to run 100 lighter-weight containers.
Bernstein says IT operating teams tend to view containers as a black box that suddenly shows up in their environment. But as IT operations gain more visibility into those containers, they will become more comfortable with deploying containers in production applications.
It may take a while for containers to be widely deployed across production applications. But as security issues surrounding containers are systematically addressed, it’s now only a matter of time before this will happen.
MV
Michael Vizard is a seasoned IT journalist, with nearly 30 years of experience writing and editing about enterprise IT issues. He is a contributor to publications including Programmableweb, IT Business Edge, CIOinsight and UBM Tech. He formerly was editorial director for Ziff-Davis Enterprise, where he launched the company’s custom content division, and has also served as editor in chief for CRN and InfoWorld. He also has held editorial positions at PC Week, Computerworld and Digital Review.