Five Burning Security Issues in Cloud Computing One of the biggest challenges with compliance is making it simple. Too many approaches to enforcing compliance require users to engage in unnatural acts that they simply are not going to do in the performance of their everyday duties. The end result is that they find a way […]

Five Burning Security Issues in Cloud Computing

One of the biggest challenges with compliance is making it simple. Too many approaches to enforcing compliance require users to engage in unnatural acts that they simply are not going to do in the performance of their everyday duties. The end result is that they find a way around the compliance requirement that in their minds gets easily justified in the name of productivity.
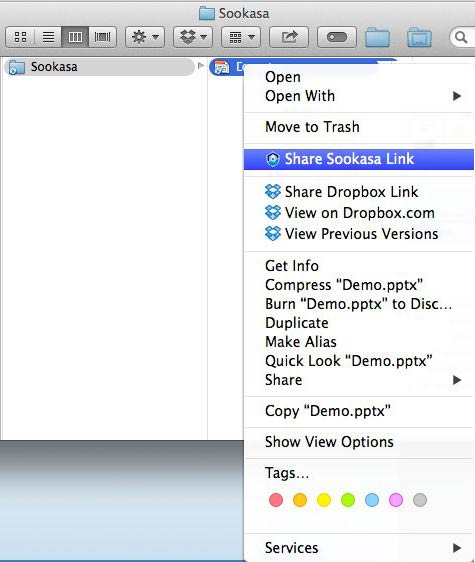
Looking to give IT organizations a simpler way to enforce compliance, Sookasa this week extended its cloud compliance service into the realm of email. Designed to provide IT organizations with a way to manage compliance via the cloud, the Sookasa Cloud Compliance Service now allows end users to access a file-sharing service via their email.
Sookasa CEO Asaf Cidon says that while many end users invoke file-sharing services such as Dropbox directly, the simplest thing for them to do is send a file via their email accounts. The Sookasa Cloud Compliance Service adds a layer of encryption to those services delivered via the cloud by making use of application programming interfaces (APIs) to integrate with a variety of file-sharing and synchronization services.
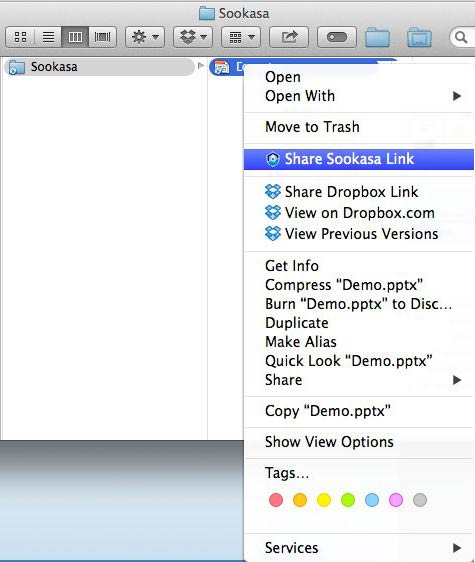
The service works by allowing end users to send a private link from within their email that allows another user to download an encrypted file. Given the fact that this file sharing is happening within the context of email and public cloud services, Cidon says that to most end users, encryption simply becomes yet another part of the cloud.
In the age of shadow IT services delivered via the cloud, IT organizations need to find ways to woo end users back into the fold. They can try to create rival file-sharing and synchronization services to provide the level of compliance required today, or they can attempt to apply encryption via a public cloud service that end users have already embraced. One of those two compliance options is not only decidedly less difficult and expensive, it also has the added benefit of not having to try to change the behavior of the end users.
MV
Michael Vizard is a seasoned IT journalist, with nearly 30 years of experience writing and editing about enterprise IT issues. He is a contributor to publications including Programmableweb, IT Business Edge, CIOinsight and UBM Tech. He formerly was editorial director for Ziff-Davis Enterprise, where he launched the company’s custom content division, and has also served as editor in chief for CRN and InfoWorld. He also has held editorial positions at PC Week, Computerworld and Digital Review.