When it comes to IT security, the odds are decidedly uneven. The perpetrators of these cyber attacks have access to what seems to be unlimited resources that they employ to automate the launch of thousands of attacks. In contrast, IT organizations are lucky if they can identify and thwart the most rudimentary of attacks—never mind anything particularly sophisticated.
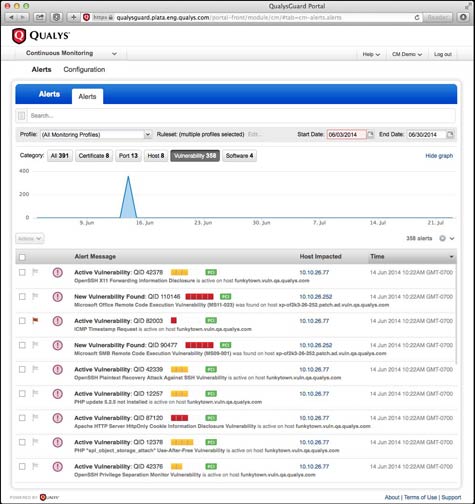
Looking to help IT organizations even the odds against hackers, Qualys today unfurled a new continuous monitoring cloud service that makes it easier to identify changes to the IT environment and send alerts to the appropriate tool for remediation.
Qualys CTO Wolfgang Kandek says that after an initial scan of the IT environment is completed, Qualys Continuous Monitoring will use subsequent scans to identify any changes to the environment. Should a change be discovered, the Qualys Continuous Monitoring service will make use of application programming interfaces (APIs) to send an alert about those changes, including changes to perimeter IP addresses or to a security information event management (SIEM) system, such as HP ArcSight or Splunk, using a Common Event Format (CEF).
Hackers and other digital miscreants are continuously scanning for system vulnerabilities. Once one is discovered, they generally change a setting on a system to make subsequent attacks more successful. In fact, it may be months before they exploit that vulnerability to the fullest extent. In much the same way that attackers are leveraging botnets and other technologies to discover those vulnerabilities, Kandek says Qualys is leveraging automated scans to discover unauthorized changes that would signal that such vulnerabilities are being exploited.
Those scans, says Kandek, can be set to run as often as an IT organization wants or the scans can be targeted to look for specific types of vulnerabilities.
IT security has clearly reached the point where reliance on manual processes isn’t going to be enough to secure the IT environment. Most organizations, however, don’t have the resources needed to continuously scan their environments. As a result, a shared cloud security service that distributes the cost of providing that level of continuous scanning is a huge help in a world where digital criminals have never been better equipped or more organized.