Seven Steps to Prepare for BYOD Most providers of IT systems management software were caught off guard by the rise in popularity of mobile computing across the enterprise. The end result is that many IT organizations have acquired separate management frameworks to manage mobile computing devices. In an ideal world, IT organizations would only have […]

Seven Steps to Prepare for BYOD

Most providers of IT systems management software were caught off guard by the rise in popularity of mobile computing across the enterprise. The end result is that many IT organizations have acquired separate management frameworks to manage mobile computing devices. In an ideal world, IT organizations would only have to buy one systems and security management framework to manage all their desktop and mobile computing devices.
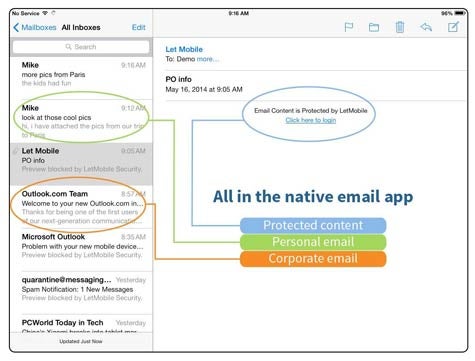
LANDESK took a significant step toward making that happen today with the acquisition of LetMobile, a provider of a secure mobile gateway for email and Web traffic that LANDESK plans to incorporate in its suite of systems management offerings.
Announced at the LANDESK Interchange 2014 conference, Stephen Brown, director of product management for mobility at LANDESK, says that unlike mobile management solutions that are focused on the device, LetMobile takes a more user-centric approach that focuses on securing enterprise data.
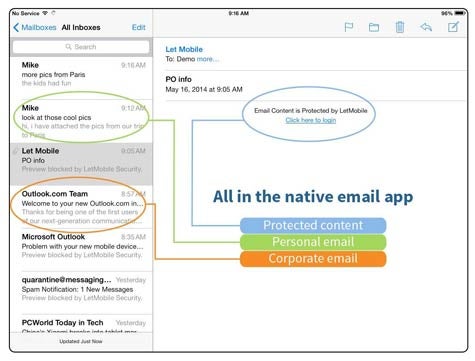
To that end, LANDESK today also announced it is making available application wrapping technology that organizations can use to secure applications, alongside providing a LetMobile mobile gateway that bi-directionally secures all the email and Web traffic between a data center and a mobile computing device without having to rely on container technology that is often too cumbersome for IT organizations to manage at scale.
Most IT organizations are struggling with finding a way to both manage and secure mobile computing devices that are proliferating across the enterprise. The challenge is that not only do users have notebooks, chances are high they are also using a tablet and a smartphone to access corporate applications. Taking a device-centric approach to managing all those devices simply isn’t practical, which means, like it or not, the time has come to find a new way to manage endpoints across the enterprise.
MV
Michael Vizard is a seasoned IT journalist, with nearly 30 years of experience writing and editing about enterprise IT issues. He is a contributor to publications including Programmableweb, IT Business Edge, CIOinsight and UBM Tech. He formerly was editorial director for Ziff-Davis Enterprise, where he launched the company’s custom content division, and has also served as editor in chief for CRN and InfoWorld. He also has held editorial positions at PC Week, Computerworld and Digital Review.